D-Link DGS-3620-52P-SI Product Manual - Page 330
Security, 802.1X
 |
View all D-Link DGS-3620-52P-SI manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 330 highlights
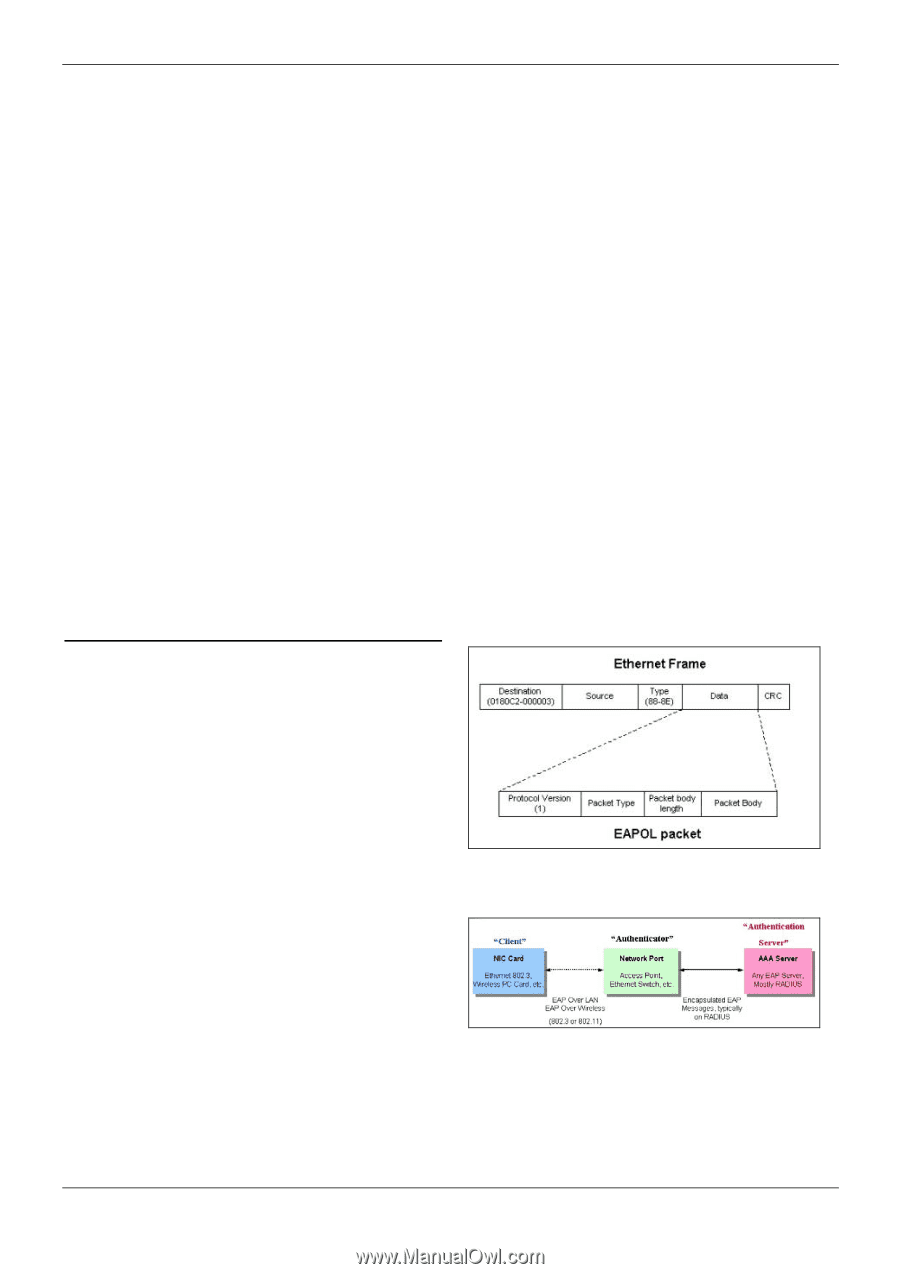
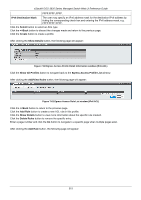
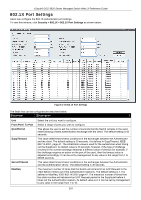
xStack® DGS-3620 Series Managed Switch Web UI Reference Guide Chapter 8 Security 802.1X RADIUS IP-MAC-Port Binding (IMPB) MAC-based Access Control (MAC) Web-based Access Control (WAC) Japanese Web-based Access Control (JWAC) Compound Authentication Port Security ARP Spoofing Prevention Settings BPDU Attack Protection Loopback Detection Settings Traffic Segmentation Settings NetBIOS Filtering Settings DHCP Server Screening Access Authentication Control SSL Settings SSH Trusted Host Settings Safeguard Engine Settings 802.1X 802.1X (Port-Based and Host-Based Access Control) The IEEE 802.1X standard is a security measure for authorizing and authenticating users to gain access to various wired or wireless devices on a specified Local Area Network by using a Client and Server based access control model. This is accomplished by using a RADIUS server to authenticate users trying to access a network by relaying Extensible Authentication Protocol over LAN (EAPOL) packets between the Client and the Server. The following figure represents a basic EAPOL packet: Figure 8-1 The EAPOL Packet Utilizing this method, unauthorized devices are restricted from connecting to a LAN through a port to which the user is connected. EAPOL packets are the only traffic that can be transmitted through the specific port until authorization is granted. The 802.1X Access Control method has three roles, each of which are vital to creating and up keeping a stable and working Access Control security method. Figure 8-2 The three roles of 802.1X The following section will explain the three roles of Client, Authenticator and Authentication Server in greater detail. 320