Cisco WS-C2960-24TT-L Software Guide - Page 192
Configuring RADIUS Authorization for User Privileged Access and Network Services, Step 1
 |
View all Cisco WS-C2960-24TT-L manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 192 highlights
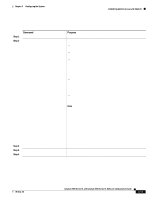
Controlling Switch Access with RADIUS Chapter 6 Configuring the System To remove the specified RADIUS server, use the no radius-server host hostname | ip-address global configuration command. To remove a server group from the configuration list, use the no aaa group server radius group-name global configuration command. To remove the IP address of a RADIUS server, use the no server ip-address server group configuration command. In this example, the switch is configured to recognize two different RADIUS group servers (group1 and group2). Group1 has two different host entries on the same RADIUS server configured for the same services. The second host entry acts as a fail-over backup to the first entry. Switch(config)# radius-server host 172.20.0.1 auth-port 1000 acct-port 1001 Switch(config)# radius-server host 172.10.0.1 auth-port 1645 acct-port 1646 Switch(config)# aaa new-model Switch(config)# aaa group server radius group1 Switch(config-sg-radius)# server 172.20.0.1 auth-port 1000 acct-port 1001 Switch(config-sg-radius)# exit Switch(config)# aaa group server radius group2 Switch(config-sg-radius)# server 172.20.0.1 auth-port 2000 acct-port 2001 Switch(config-sg-radius)# exit Configuring RADIUS Authorization for User Privileged Access and Network Services AAA authorization limits the services available to a user. When AAA authorization is enabled, the switch uses information retrieved from the user's profile, which is in the local user database or on the security server, to configure the user's session. The user is granted access to a requested service only if the information in the user profile allows it. You can use the aaa authorization global configuration command with the radius keyword to set parameters that restrict a user's network access to privileged EXEC mode. The aaa authorization exec radius local command sets these authorization parameters: • Use RADIUS for privileged EXEC access authorization if authentication was performed by using RADIUS. • Use the local database if authentication was not performed by using RADIUS. Note Authorization is bypassed for authenticated users who log in through the CLI even if authorization has been configured. Beginning in privileged EXEC mode, follow these steps to specify RADIUS authorization for privileged EXEC access and network services: Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Command configure terminal aaa authorization network {default | list-name} group radius aaa authorization exec {default | list-name} group radius end show running-config copy running-config startup-config Purpose Enter global configuration mode. Configure the switch for user RADIUS authorization for all network-related service requests. Configure the switch for user RADIUS authorization to determine if the user has privileged EXEC access. The exec keyword might return user profile information (such as autocommand information). Return to privileged EXEC mode. Verify your entries. (Optional) Save your entries in the configuration file. 6-64 Catalyst 2900 Series XL and Catalyst 3500 Series XL Software Configuration Guide 78-6511-08