HP CM8000 Practical IPsec Deployment for Printing and Imaging Devices - Page 42
IKE Phase 1: Accepted, IKE Phase 1: Diffie-Hellman Key Exchange
 |
View all HP CM8000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 42 highlights
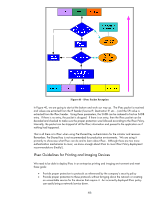
Here we see the IKE Phase 1 main mode negotiation where the host is sending HP Jetdirect the list of transforms it wants to support. In Figure 34, HP Jetdirect accepts one. Figure 34 - IKE Phase 1: Accepted Now we begin the Diffie-Hellman key exchange in Figure 35. Figure 35 - IKE Phase 1: Diffie-Hellman Key Exchange And in Figure 36, we begin the Authentication process, which in this example is using Pre-Shared Key. 42

42
Here we see the IKE Phase 1 main mode negotiation where the host is sending HP Jetdirect the list of
transforms it wants to support.
In Figure 34, HP Jetdirect accepts one.
Figure 34 – IKE Phase 1: Accepted
Now we begin the Diffie-Hellman key exchange in Figure 35.
Figure 35 – IKE Phase 1: Diffie-Hellman Key Exchange
And in Figure 36, we begin the Authentication process, which in this example is using Pre-Shared
Key.