TP-Link TL-SG2008 TL-SG2008 V1 User Guide 1910010984 - Page 121
Application Example for ACL, Configuration Procedure
 |
View all TP-Link TL-SG2008 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 121 highlights
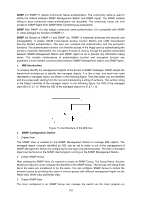
The following entries are displayed on this screen: ¾ VLAN-Bind Config Policy Name: Select the name of the policy you want to bind. VLAN ID: Enter the ID of the VLAN you want to bind. ¾ VLAN-Bind Table Index: Displays the index of the binding policy. Policy Name: Displays the name of the binding policy. VLAN ID: Displays the ID of the VLAN bound to the corresponding policy. Direction: Displays the binding direction. Configuration Procedure: Step Operation Description 1 Configure ACL rules Required. On ACL→ACL Config configuration pages, configure ACL rules to match packets. 2 Configure Policy Required. On ACL→Policy Config configuration pages, configure the policy to control the data packets those match the corresponding ACL rules. 3 Bind the policy to the Required. On ACL→Policy Binding configuration pages, port/VLAN bind the policy to the port/VLAN to make the policy effective on the corresponding port/VLAN. 10.4 Application Example for ACL ¾ Network Requirements 1. The manager of the R&D department can access to the forum of the company. The MAC address of the manager is 00-64-A5-5D-12-C3. 2. The staff of the R&D department can visit the forum. 3. The staff of the marketing department can not visit the forum. 4. The R&D department and marketing department can not communicate with each other. 114