Cisco WS-C2960-24TC-S Software Guide - Page 178
ip http secure-ciphersuite, rc4-128-md5 - l end of life
 |
View all Cisco WS-C2960-24TC-S manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 178 highlights
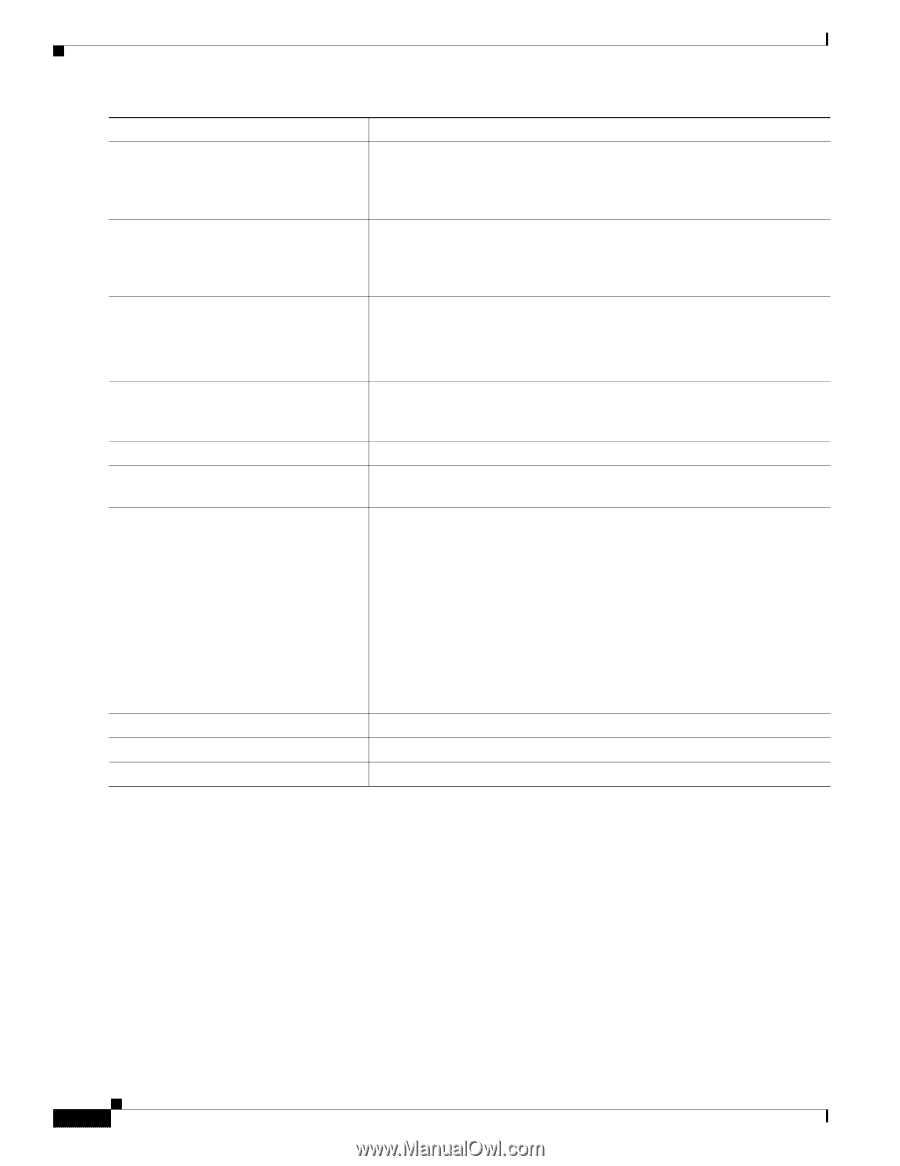
Configuring the Switch for Secure Socket Layer HTTP Chapter 8 Configuring Switch-Based Authentication Command Purpose Step 5 ip http secure-ciphersuite {[3des-ede-cbc-sha] [rc4-128-md5] [rc4-128-sha] [des-cbc-sha]} (Optional) Specify the CipherSuites (encryption algorithms) to be used for encryption over the HTTPS connection. If you do not have a reason to specify a particularly CipherSuite, you should allow the server and client to negotiate a CipherSuite that they both support. This is the default. Step 6 ip http secure-client-auth (Optional) Configure the HTTP server to request an X.509v3 certificate from the client for authentication during the connection process. The default is for the client to request a certificate from the server, but the server does not attempt to authenticate the client. Step 7 ip http secure-trustpoint name Specify the CA trustpoint to use to get an X.509v3 security certificate and to authenticate the client certificate connection. Note Use of this command assumes you have already configured a CA trustpoint according to the previous procedure. Step 8 ip http path path-name (Optional) Set a base HTTP path for HTML files. The path specifies the location of the HTTP server files on the local system (usually located in system flash memory). Step 9 ip http access-class access-list-number (Optional) Specify an access list to use to allow access to the HTTP server. Step 10 ip http max-connections value (Optional) Set the maximum number of concurrent connections that are allowed to the HTTP server. The range is 1 to 16; the default value is 5. Step 11 ip http timeout-policy idle seconds life (Optional) Specify how long a connection to the HTTP server can remain seconds requests value open under the defined circumstances: • idle-the maximum time period when no data is received or response data cannot be sent. The range is 1 to 600 seconds. The default is 180 seconds (3 minutes). • life-the maximum time period from the time that the connection is established. The range is 1 to 86400 seconds (24 hours). The default is 180 seconds. • requests-the maximum number of requests processed on a persistent connection. The maximum value is 86400. The default is 1. Step 12 end Return to privileged EXEC mode. Step 13 show ip http server secure status Display the status of the HTTP secure server to verify the configuration. Step 14 copy running-config startup-config (Optional) Save your entries in the configuration file. Use the no ip http server global configuration command to disable the standard HTTP server. Use the no ip http secure-server global configuration command to disable the secure HTTP server. Use the no ip http secure-port and the no ip http secure-ciphersuite global configuration commands to return to the default settings. Use the no ip http secure-client-auth global configuration command to remove the requirement for client authentication. To verify the secure HTTP connection by using a Web browser, enter https://URL, where the URL is the IP address or hostname of the server switch. If you configure a port other than the default port, you must also specify the port number after the URL. For example: https://209.165.129:1026 or https://host.domain.com:1026 8-42 Catalyst 2960 Switch Software Configuration Guide OL-8603-04