Dell PowerConnect W-Series FIPS Dell PowerConnect W-6000M3 and W-3000 Controll - Page 19
CSPs Used in Aruba Controllers
 |
View all Dell PowerConnect W-Series FIPS manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 19 highlights
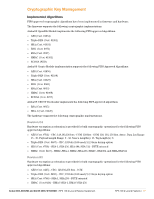
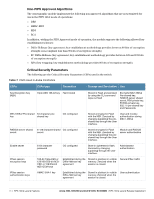
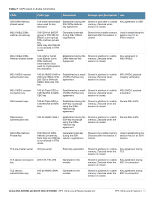
Table 7 CSPs Used in Aruba Controllers CSPs CSPs type Generation Storage and Zeroization Use SSH Diffie-Hellman shared secret 128-octet intermediate Established during the Stored in plain text in volatile Key agreement in SSH value used for key SSH Diffie-Hellman memory, Zeroized when derivation key agreement session is closed. IKEv1/IKEv2 DiffieHellman private key 768/1024-bit (MODP group) or 256/384-bit (Elliptic curve group) Diffie-Hellman private key. Note: Key size 768 bits is not allowed in FIPS mode. Generated internally during IKEv1/IKEv2 negotiations Stored in the volatile memory. Used in establishing the Zeroized after the session is session key for an closed. IPSec session IKEv1/IKEv2 DiffieHellman shared secret 128 octet or 32/48 octet (Elliptic curve Diffie Hellman) intermediate value used for cryptographic key derivation Established during the Diffie-Hellman Key Agreement Stored in plaintext in volatile memory. Zeroized when session is closed. Key agreement in IKEv1/IKEv2 IKEv1/IKEv2 session authentication key 160-bit HMAC-SHA1or 256 byte HMAC-SHA256-128 or 384 byte HMAC-SHA-384-192 key Established as a result of Diffie-Hellman key agreement. Stored in plaintext in volatile memory. Zeroized when session is closed. IKEv1/IKEv2 payload integrity verification IKEv1/IKEv2 session encryption key 168-bit Triple-DES or 128/192/256-bit AESCBC key Established as a result Stored in plaintext in volatile of Diffie-Hellman key memory. Zeroized when agreement. session is closed. IKEv1/IKEv2 payload encryption SSH session keys 168-bit Triple-DES or 128/192/256-bit AES keys Established during the SSH key exchange using the DiffieHellman key agreement Stored in plaintext in volatile memory. Zeroized when the session is closed. Secure SSH traffic SSH session authentication key 160-bit HMAC-SHA-1 Established during the SSH key exchange using the DiffieHellman key agreement Stored in plaintext in volatile memory. Zeroized when the session is closed. Secure SSH traffic SSH Diffie-Hellman Private Key 768/1024-bit DiffieHellman private key. Note: Key size 768 bits is not allowed in FIPS mode. Generated internally during the SSH session negotiations Stored in the volatile memory. Used in establishing the Zeroized after the session is session key for an SSH closed. session. TLS pre-master secret 48 byte secret Externally generated Stored in plaintext in volatile memory. Zeroized when the session is closed. Key agreement during TLS TLS session encryption AES 128, 192, 256 key Generated in the module Stored in plaintext in volatile memory. Zeroized when the session is closed. Key agreement during 802.1x connection TLS session authentication key 160-bit HMAC-SHA1 Generated in the key module Stored in plaintext in volatile memory. Zeroized when the session is closed. Key agreement during 802.1x connection Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 19