Dell PowerConnect W-Series FIPS Dell PowerConnect W-6000M3 and W-3000 Controll - Page 20
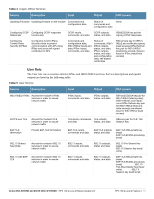
CSPs type, Generation, Storage and Zeroization
 |
View all Dell PowerConnect W-Series FIPS manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 20 highlights
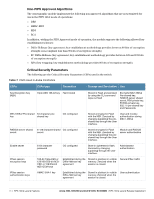
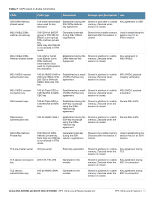
Table 7 CSPs Used in Aruba Controllers CSPs CSPs type Generation Storage and Zeroization Use RSA Private Key RSA 1024/2048 bit key Generated in the module Stored in flash memory encrypted with KEK. Zeroized by the CO command write erase all. Used by TLS and EAPTLS/PEAP protocols during the handshake, used for signing OCSP responses, and used by IKEv1/IKEv2 for device authentication and for signing certificates ECDSA Private Key ECDSA suite B P-256 Generated in the and P-384 curves module Stored in flash memory encrypted with KEK. Zeroized by the CO command write erase all. Used by TLS and EAPTLS/PEAP protocols during the handshake. skeyid Intermediate 160-bit/ 256-byte/384-byte value used in key derivation Established during the Stored in plaintext in volatile Diffie-Hellman Key memory. Zeroized when Agreement session is closed. Key agreement in IKEv1/IKEv2 skeyid_d Intermediate 160-bit/ 256-byte/384-byte value used in key derivation Established during the Stored in plaintext in volatile Diffie-Hellman Key memory. Zeroized when Agreement session is closed. Key agreement in IKEv1/IKEv2 802.11i Pre-Shared Key 802.11i pre-shared (PSK) secret key (256-bit) CO configured Stored in flash memory encrypted with KEK. Zeroized by the CO command write erase all. Used by the 802.11i protocol 802.11i Pair-Wise Master key (PMK) 802.11i secret key (256-bit) Derived during the EAP-TLS/PEAP handshake Stored in the volatile memory. Used by the 802.11i Zeroized on reboot. protocol 802.11i session key AES-CCM key (128 bit), AES-GCM key (128/256-bit) Derived from 802.11 PMK Stored in plaintext in volatile Used for 802.11i memory. Zeroized on reboot. encryption Data link (Layer 2) encryption key AES key (256 bit) Derived during the Stored in plaintext in volatile Used to encrypt EAP-TLS handshake memory. Zeroized on reboot. tunneled Layer 2 frames Data link (Layer 2) integrity key HMAC-SHA1 key (160bit) Derived during EAPTLS handshake storage and zeroization: Stored in plaintext in volatile memory Stored in plaintext in volatile Used to integritymemory. Zeroized on reboot. protect tunneled Layer 2 frames Passwords 6-character password CO configured Stored encrypted in Flash with KEK. Zeroized by either deleting the password configuration file or by overwriting the password with a new one. Authentication for accessing the management interfaces, RADIUS authentication ArubaOS OpenSSL RNG Seed for FIPS compliant ANSI X9.31, Appendix A2.4 using AES-128 key algorithm Seed (16 bytes) Derived using NONFIPS approved HW RNG (/dev/urandom) Stored in plaintext in volatile memory only. Zeroized on reboot. Seed ANSI X9.31 RNG 20 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement