Lenovo ThinkPad T41p IBM System Information Center Administrator's Guide - Page 19
password-protected
 |
View all Lenovo ThinkPad T41p manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 19 highlights
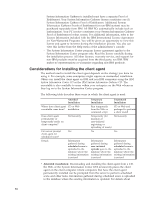
- Create new passwords as expired so that users must change after first logon: Mark this check box to require users to establish their own password after receiving the computer-generated password. - Expire passwords after XX days: Mark this check box and then type the maximum number of days a password is accepted. (Default is 186 days, or approximately six months.) v Under Password Creation Rules, mark the check box for Enable password rule checking if the creation of passwords must follow certain rules; then respond to the following options: - Passwords must contain: Mark a check box for the type of characters (non-numeric, numeric, or non-alphanumeric) a password must contain. (Default is non-numeric and numeric.) - Minimum length: Type the minimum length of the password. (Default is 6.) - Maximum length: Type the maximum length of the password. (Default is 15.) - Maximum number of matching sequential characters: Type the maximum number of sequential password characters that can match. (Default is 2.) - Maximum number of sequential characters reused from previous password: Type the maximum number of sequential password characters that can be reused in a new password. (Default is 3.) 10. Click Next. The Form Settings window opens. 11. The Form Settings window displays fields you can select as ″required″ in order for an asset or user to be successfully added to the database. These are fields that users must complete during the asset registration process before adding an asset or uploading an asset scan. Default settings are provided. You can restore defaults by clicking the Defaults button. v The Asset Demographics Form includes information specific to the asset. Mark the check box for all fields required at the time the asset is registered. v The User Demographics Form includes information specific to the user. Mark the check box for all fields required at the time the asset is registered. 12. Click Next. The Security Settings window opens. 13. In the Security Settings window, you can choose to have the following options enabled. These options are helpful if you want to use the security report that lists all assets that are in violation of security policies. v Verify that all File Shares on client computers are password-protected: Mark this check box if you want the System Information Center program to check and verify that all file shares on client computers are password-protected each time the asset is revised. v Verify that all Windows screen savers are password-protected: Mark this check box if you want the System Information Center program to check and verify that the Windows screen saver password is set on all client computers each time the asset is revised. v Verify that all Windows accounts are password-protected: Mark this check box if you want the System Information Center program to check and verify that the Windows account password is set on all client computers each time the asset is revised. v Windows accounts require passwords: Mark this check box if you want the System Information Center program to check and verify that the Windows Chapter 2. Installing the System Information Center program on a server 11