HP AE370A Brocade Fabric OS Command Reference Manual v6.2.0 (53-1001186-01, Ap - Page 143
cryptoCfg, 3. High Availability HA cluster configuration
 |
UPC - 882780362611
View all HP AE370A manuals
Add to My Manuals
Save this manual to your list of manuals |
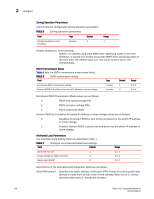
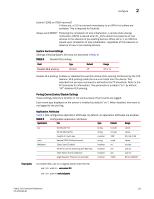
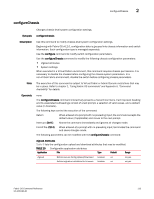
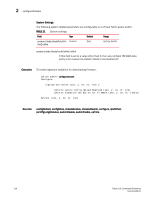
Page 143 highlights
cryptoCfg 2 cryptoCfg Name Performs encryption configuration and management functions. Synopsis cryptocfg --help -nodecfg cryptocfg --help -groupcfg cryptocfg --help -hacluster cryptocfg --help -devicecfg cryptocfg --help -transcfg Description Use the cryptoCfg command to configure and manage the Brocade Encryption Switch and the FS8-18 encryption blade. These platforms support the encryption of data-at-rest for tape devices and disk array logical unit numbers (LUNs). The cryptoCfg CLI consists of five command sets grouped around the following configuration functions: "1. Node configuration" on page 116 "2. Encryption group configuration" on page 121 "3. High Availability (HA) cluster configuration" on page 128 "4. Storage device configuration and management" on page 131 "5. Transaction management" on page 148 Each of these command groups is documented in a separate section that includes function, synopsis, description, and operands. Examples are presented at the end of the help page. For detailed encryption switch management and configuration procedures, refer to the Fabric OS Encryption Administrator's Guide. CAUTION When configuring a LUN with multiple paths, there is a considerable risk of ending up with potentially catastrophic scenarios where different policies exist for each path of the LUN, or a situation where one path ends up being exposed through the encryption switch and other path has direct access to the device from a host outside the secured realm of the encryption platform. To protect against this risk, it is necessary to configure containers IN SEQUENCE and with the same policies and not issue a commit until the configuration for all hosts accessing the LUN is complete. Failure to follow correct configuration procedures for multi-path LUNs results in data corruption. If you are configuring multi-path LUNs as part of a HA cluster or DEK cluster or as a standalone LUN accessed by multiple hosts, follow the instructions described in the section "Configuring a multi-path Crypto LUN" in the Fabric OS Encryption Administrator's Guide. Note The execution of this command is subject to Virtual Fabric or Admin Domain restrictions that may be in place. For details on command availability, refer to Appendix A, "Appendix A: Command availability" on page 849. Fabric OS Command Reference 115 53-1001186-01