ZyXEL P-661HW-61 User Guide - Page 238
Telecommuters Sharing One VPN Rule Example, Table 67
 |
View all ZyXEL P-661HW-61 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 238 highlights
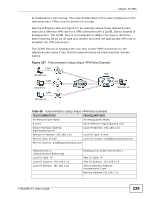
Chapter 16 VPN 16.6.11.1 Telecommuters Sharing One VPN Rule Example See the following figure and table for an example configuration that allows multiple telecommuters (A, B and C in the figure) to use one VPN rule to simultaneously access a ZyXEL Device at headquarters (HQ in the figure). The telecommuters do not have domain names mapped to the WAN IP addresses of their IPSec routers. The telecommuters must all use the same IPSec parameters but the local IP addresses (or ranges of addresses) should not overlap. Figure 106 Telecommuters Sharing One VPN Rule Example LAN A 192.168.2.12 B LAN 192.168.3.2 C LAN HQ LAN 192.168.1.10 192.168.4.15 Table 67 Telecommuters Sharing One VPN Rule Example FIELDS TELECOMMUTERS HEADQUARTERS My IP Address: 0.0.0.0 (dynamic IP address assigned by the ISP) Public static IP address Secure Gateway Public static IP address IP Address: 0.0.0.0 With this IP address only the telecommuter can initiate the IPSec tunnel. Local IP Address: Telecommuter A: 192.168.2.12 Telecommuter B: 192.168.3.2 Telecommuter C: 192.168.4.15 192.168.1.10 Remote IP Address: 192.168.1.10 0.0.0.0 (N/A) 16.6.11.2 Telecommuters Using Unique VPN Rules Example In this example the telecommuters (A, B and C in the figure) use IPSec routers with domain names that are mapped to their dynamic WAN IP addresses (use Dynamic DNS to do this). With aggressive negotiation mode (see Section 16.6.6 on page 234), the ZyXEL Device can use the ID types and contents to distinguish between VPN rules. Telecommuters can each use a separate VPN rule to simultaneously access a ZyXEL Device at headquarters. They can use different IPSec parameters. The local IP addresses (or ranges of addresses) of the rules configured on the ZyXEL Device 238 P-661HNU-Fx User's Guide