Belkin F5D9630uk4A F5D9630-4A User Manual - United Kingdom - Page 40
Encryption/Security
 |
View all Belkin F5D9630uk4A manuals
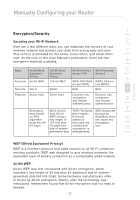
Add to My Manuals
Save this manual to your list of manuals |
Page 40 highlights
Manually Configuring your Router section 1 Encryption/Security Securing your Wi-Fi Network 2 Here are a few different ways you can maximize the security of your wireless network and protect your data from prying eyes and ears. 3 This section is intended for the home, home office, and small office user. At the time of this User Manual's publication, there are four encryption methods available. 4 Name 64-Bit Wired 128-Bit Wired Wi-Fi Protected Wi-Fi Protected 5 Equivalent Equivalent Access-TKIP Access 2 Privacy Privacy 6 Acronym 64-bit WEP 128-bit WEP WPA-TKIP/AES WPA2-AES (or (or just WPA) just WPA2) Security Good Better Best Best 7 Features Static keys Static keys Dynamic key Dynamic key encryption encryption 8 and mutual and mutual authentication authentication 9 Encryption More secure TKIP (Temporal AES (Advanced keys based than 64-bit Key Integrity Encryption on RC4 algorithm WEP using a key length of Protocol) added so Standard) does not cause any 10 (typically 40- 104 bits plus that keys are throughput bit keys) 24 additional rotated and loss bits of system- encryption is 11 generated data strengthened 12 WEP (Wired Equivalent Privacy) WEP is a common protocol that adds security to all Wi-Fi-compliant wireless products. WEP was designed to give wireless networks the equivalent level of privacy protection as a comparable wired network. 64-Bit WEP 64-bit WEP was first introduced with 64-bit encryption, which includes a key length of 40 bits plus 24 additional bits of systemgenerated data (64 bits total). Some hardware manufacturers refer to 64-bit as 40-bit encryption. Shortly after the technology was introduced, researchers found that 64-bit encryption was too easy to decode. 37