D-Link DES-3852 Product Manual - Page 160
xStack DES-3800 Series Layer 3 Stackable Fast Ethernet Managed Switch CLI Manual, mirror
 |
UPC - 790069289460
View all D-Link DES-3852 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 160 highlights
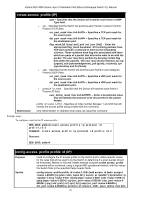
xStack DES-3800 Series Layer 3 Stackable Fast Ethernet Managed Switch CLI Manual config access_profile profile_id (packet content mask) of the command. This value will over-write the value in the DSCP field of the packet. deny - Specifies that packets that match the access profile are not permitted to be forwarded by the Switch and will be filtered. mirror - Selecting mirror specifies that packets that match the access profile are mirrored to a port defined in the config mirror port command. Port Mirroring must be enabled and a target port must be set. Remember, Port Mirroring cannot crossbox, that is they cannot span across switches in a switch stack. delete access_id − Use this command to delete a specific rule from the packet content mask profile. Up to 65535 rules may be specified for the Packet Content access profile. Restrictions Only Administrator or Operator-level users can issue this command. Example usage: To create an access profile by packet content mask: DES-3800:admin# config access_profile profile_id 3 add access_id 1 packet_content offset_0-15 0x11111111 0x11111111 0x11111111 0x11111111 offset_16-31 0x11111111 0x11111111 0x11111111 0x11111111 port 1 deny Command: config access_profile profile_id 3 add access_id 1 packet_content offset_0-15 0x11111111 0x11111111 0x11111111 0x11111111 offset_16-31 0x11111111 0x11111111 0x11111111 0x11111111 port 1 deny Success. DES-3800:admin# NOTE: Address Resolution Protocol (ARP) is the standard for finding a host's hardware address (MAC Address). However, ARP is vulnerable as it can be easily spoofed and utilized to attack a LAN (known as ARP spoofing attack). For a more detailed explaination on how ARP protocol works and how to employ D-Link's advanced unique Packet Content ACL to prevent ARP spoofing attack, please see Appendix B, at the end of this manual. 156