HP AE370A HP StorageWorks Fabric OS 6.2 administrator guide (5697-0016, May 20 - Page 154
ipsecconfig --add policy ips selector -t SELECTOR-OUT
 |
UPC - 882780362611
View all HP AE370A manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 154 highlights
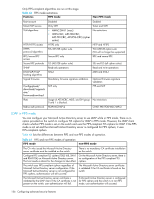
See Chapter 3, "Configuring standard security features" on page 99 for information on how to set up pre-shared keys and certificates. 7. Configure the IKE policy using the ipSecConfig --add policy ike -tag name -remote IP_address[/prefixlength] -id IP_address[/prefixlength] -remoteid IP_address[/prefixlength] -enc algorithm -hash algorithm -prf algorithm -auth psk|dss|rsasig -dh number -psk file command. The following example creates an IKE policy for the remote peer. switch:admin> ipsecconfig --add policy ike -t IKE01 -remote 10.33.74.13 \ -id 10.33.69.132 -remoteid 10.33.74.13 -enc 3des_cbc \ -hash hmac_md5 -prf hmac_md5 -auth psk -dh modp1024 \ -psk ipseckey.psk 8. Create an IPsec transform on each switch using the ipSecConfig --add policy ips transform -tag name -mode tunnel|transport -sa-proposal name -action discard|bypass|protect -ike name command. The following example creates an IPsec transform TRANSFORM01 to use the transport mode to protect traffic identified for IPsec protection and use IKE01 as key management policy. switch:admin> ipsecconfig --add policy ips transform -t TRANSFORM01 \ -mode transport -sa-proposal IPSEC-AH \ -action protect -ike IKE01 9. Create a traffic selector on each switch using the ipSecConfig --add policy ips selector -tag name -direction in| out -local IP_address[/prefixlength] -remote IP_address[/prefixlength] -transform name command. The example below create a traffic selector to select outbound and inbound traffic that needs to be protected. switch:admin> ipsecconfig --add policy ips selector -t SELECTOR-OUT \ -d out -l 10.33.74.13 -r 10.33.69.132 -transform TRANSFORM01 switch:admin> ipsecconfig --add policy ips selector -t SELECTOR-IN \ -d in -l 10.33.69.132 -r 10.33.74.13 -t transform TRANSFORM01 10. Verify that traffic is protected: a. Initiate a telnet, SSH, or ping session from the two switches. b. Verify that IP traffic is encapsulated. c. Monitor IPsec SAs created using IKE for the above traffic flow: • Use the ipsecConfig --show manual-sa -a command with the operands specified to display the outbound and inbound SAs in kernel SADB. • Use the ipsecConfig --show policy ips sa -a command with the specified operands to display all IPsec SA policies. • Use the ipsecConfig --show policy ips sa-proposal -a command with the specified operands to display IPsec proposals. • Use the ipsecConfig --show policy ips transform -a command with the specified operands to display IPsec transforms. • Use the ipsecConfig --show policy ips selector -a command with the specified operands to display IPsec traffic selectors. • Use the ipsecConfig --show policy ike -a command with the specified operands to display IKE policies. • Use the ipsecConfig --flush manual-sa command with the specified operands to flush the created SAs in the kernel SADB. 152 Configuring advanced security features