HP AE370A HP StorageWorks Fabric OS 6.2 administrator guide (5697-0016, May 20 - Page 162
Enabling FIPS mode
 |
UPC - 882780362611
View all HP AE370A manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 162 highlights
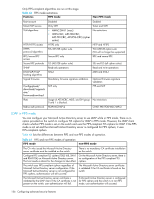
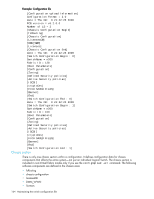
Enabling FIPS mode 1. Log in to the switch using an account assigned the admin or securityAdmin role. 2. Optional: Select the appropriate method based on your needs: • If the switch is set for RADIUS, modify each server to use only peap-mschapv2 as the authentication protocol using the aaaConfig --change or aaaConfig --remove command. • If the switch is set for LDAP, see the instructions in "Setting up LDAP for FIPS mode" on page 157. 3. Optional: Set the authentication protocols. a. Enter the following command to set the hash type for MD5 which is used in authentication protocols DHCHAP and FCAP: authutil --set -h sha1 b. Set the DH group to 1 or 2 or 3 or 4 using authUtil --set -g , where the DH group is represented by . 4. Install the LDAP CA certificate on the switch and Microsoft Active Directory server. See the instructions "LDAP certificates for FIPS mode" on page 158. 5. Block Telnet, HTTP, and RPC using the ipfilter policy command for each protocol: a. Create an IP filter rule for each policy/protocol, see "Creating an IP Filter policy" on page 135. b. Add a rule to the IP filter policy, see "Adding a rule to an IP Filter policy" on page 138. You can use the following modifications to the rule: ipfilter --addrule -rule -sip -dp -proto -act • -sip option can be given as any • -dp option for the port numbers for Telnet, HTTP, and RPC are 23, 80, and 898 respectively • -proto option should be set to tcp c. Activate the IP filter policy/protocol, see "Activating an IP Filter policy" on page 136. d. Save the IP filter policy/protocol, see "Saving an IP Filter policy" on page 136. Example ipfilter --createrule http_block_v4 --type ipv4 ipfilter --addrule http_block_v4 -rule 2 -sip any -dp 80 -proto tcp -act deny ipfilter --activate http_block_v4 ipfilter --save http_block_v4 6. Enter the following command to block access to the boot PROM: fipscfg --disable bootprom Block boot PROM access before disabling the root account. 7. Enable signed firmware by typing the configure command and respond to the prompts as follows: System services No cfgload attributes Yes Enforce secure config Upload/Download Press Enter to accept the default. Enforce firmware signature validation Yes Example: Adding a rule to the IP filter policy switch:admin> configure Not all options will be available on an enabled switch. To disable the switch, use the "switchDisable" command. Configure... System services (yes, y, no, n): [no] ... cfgload attributes (yes, y, no, n): [no] yes Enforce secure config Upload/Download (yes, y, no, n): [no] Enforce firmware signature validation (yes, y, no, n): [no] yes 160 Configuring advanced security features