Ricoh Aficio MP 2851 Security Target - Page 30
Organisational Security Policies and 3.3 Assumptions.
 |
View all Ricoh Aficio MP 2851 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 30 highlights
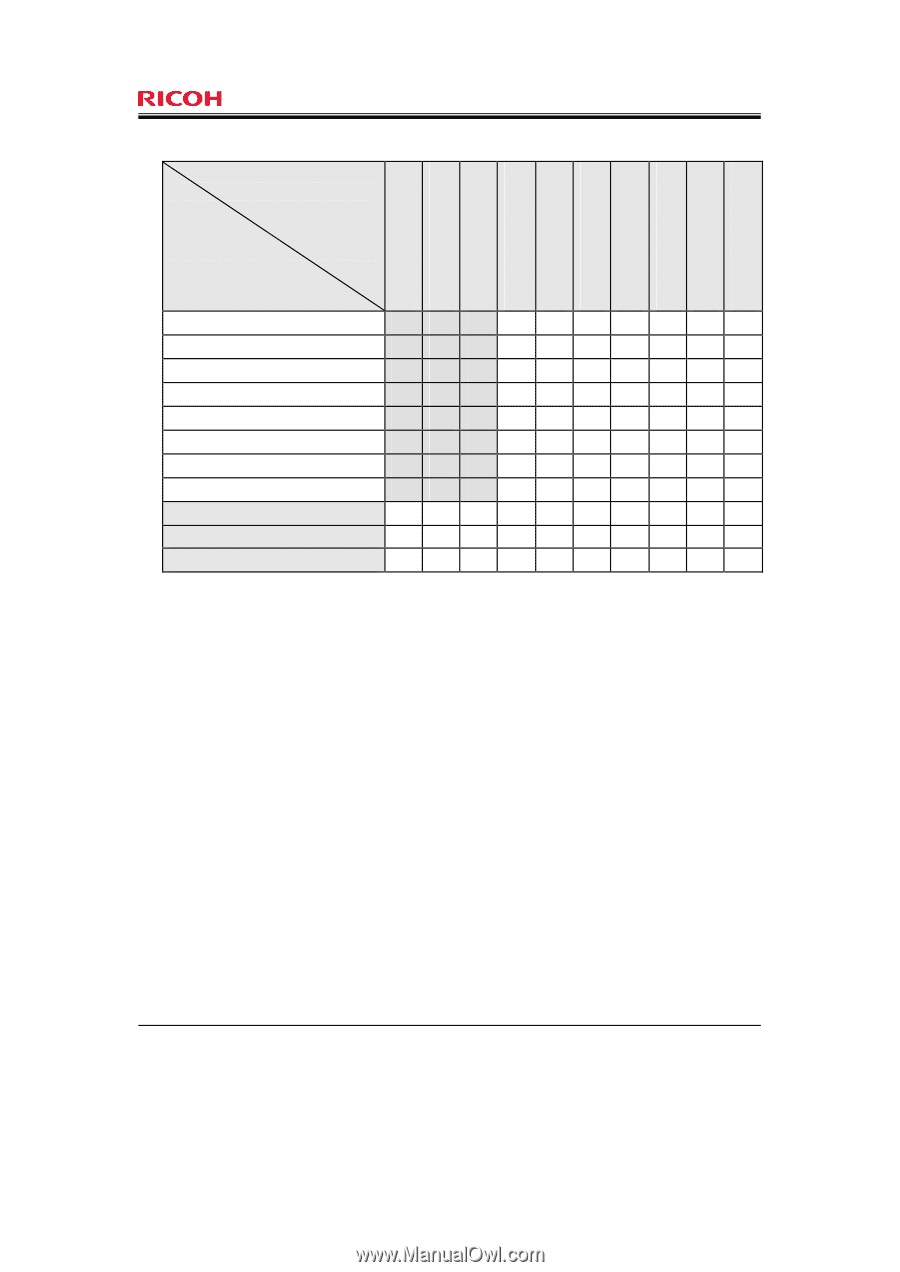
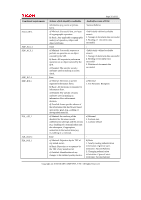
Page 30 of 81 Table 3: Relationship between security environment and security objectives TOE security Environment A.ADMIN A.SUPERVISOR A.NETWORK T.ILLEGAL_USE T.UNAUTH_ACCESS T.ABUSE_SEC_MNG T.SALVAGE T.TRANSIT T.FAX_LINE P.SOFTWARE Security objectives O.AUDIT O.I&A O.DOC_ACC O.MANAGE O.MEM.PROTECT O.NET.PROTECT O.GENUINE O.LINE_PROTECT OE.ADMIN OE.SUPERVISOR OE.NETWORK v vv vv v vv v v v v v v v v v 4.3.2 Tracing Justification The following are the rationale for each security objectives being appropriate to satisfy "3.1 Threats", "3.2 Organisational Security Policies" and "3.3 Assumptions". A.ADMIN (Assumptions for administrators) As specified by A.ADMIN, administrators shall have sufficient knowledge to operate the TOE securely in the roles assigned to them and instruct general users to operate the TOE securely also. Additionally, administrators are unlikely to abuse their permissions. As specified by OE.ADMIN, the responsible manager of the MFP shall select trusted persons as administrators and instruct them on their administrator roles. Once instructed, administrators thenshall instruct general users, familiarising them with the compliance rules for secure TOE operation as defined in the administrator guidance for the TOE. Therefore, A.ADMIN is upheld. A.SUPERVISOR (Assumptions for supervisors) As specified by A.SUPERVISOR, supervisors shall have sufficient knowledge to operate the TOE securely in the roles assigned to them, and be unlikely to abuse their permissions. As specified by OE.SUPERVISOR, the responsible manager of the MFP shall select trusted persons as supervisors and instruct them on the role of supervisor. Therefore, A.SUPERVISOR is upheld. Copyright (c) 2010 RICOH COMPANY, LTD. All Rights Reserved.