TP-Link TL-SG5412F TL-SG5412F V1 User Guide - Page 167
ARP Detect
 |
View all TP-Link TL-SG5412F manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 167 highlights
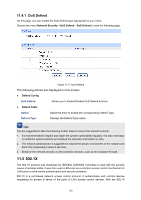
ARP Flooding Attack The attacker broadcasts a mass of various fake ARP packets in a network segment to occupy the network bandwidth viciously, which results in a dramatic slowdown of network speed. Meantime, the Gateway learns the false IP address-to-MAC address mapping entries from these ARP packets and updates its ARP table. As a result, the ARP table is fully occupied by the false entries and unable to learn the ARP entries of legal Hosts, which causes that the legal Hosts can not access the external network. The IP-MAC Binding function allows the switch to bind the IP address, MAC address, VLAN ID and the connected Port number of the Host together when the Host connects to the switch. Based on the predefined IP-MAC Binding entries, the ARP Inspection functions to detect the ARP packets and filter the illegal ARP packet so as to prevent the network from ARP attacks. The ARP Inspection function is implemented on the ARP Detect, ARP Defend and ARP Statistics pages. 11.2.1 ARP Detect ARP Detect feature enables the switch to detect the ARP packets based on the bound entries in the IP-MAC Binding Table and filter the illegal ARP packets, so as to prevent the network from ARP attacks, such as the Network Gateway Spoofing and Man-In-The-Middle Attack, etc. Choose the menu Network Security→ARP Inspection→ARP Detect to load the following page. Figure 11-13 ARP Detect The following entries are displayed on this screen: ARP Detect ARP Detect: Enable/Disable the ARP Detect function, and click the Apply button to apply. Trusted Port Trusted Port: Select the port for which the ARP Detect function is unnecessary as the Trusted Port. The specific ports, such as up-linked port, routing port and LAG port, should be set as Trusted Port. To ensure the normal communication of the switch, please configure the ARP Trusted Port before enabling the ARP Detect function. 158