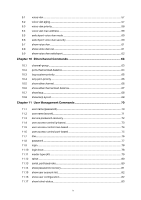
Chapter 12
HTTP and HTTPS Commands
..................................................................
84
12.1
ip http server
..................................................................................................................................
84
12.2
ip http max-users
..........................................................................................................................
85
12.3
ip http session timeout
...............................................................................................................
86
12.4
ip http secure-server
...................................................................................................................
86
12.5
ip http secure-protocol
...............................................................................................................
87
12.6
ip http secure-ciphersuite
.........................................................................................................
88
12.7
ip http secure-max-users
..........................................................................................................
88
12.8
ip http secure-session timeout
................................................................................................
89
12.9
ip http secure-server download certificate
.........................................................................
90
12.10
ip http secure-server download key
......................................................................................
91
12.11
show ip http configuration
.........................................................................................................
92
12.12
show ip http secure-server
.......................................................................................................
92
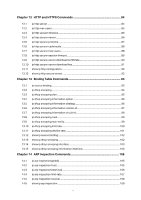
Chapter 13
Binding Table Commands
.........................................................................
93
13.1
ip source binding
..........................................................................................................................
93
13.2
ip dhcp snooping
..........................................................................................................................
94
13.3
ip dhcp snooping vlan
.................................................................................................................
95
13.4
ip dhcp snooping information option
.....................................................................................
96
13.5
ip dhcp snooping information strategy
.................................................................................
96
13.6
ip dhcp snooping information remote-id
..............................................................................
97
13.7
ip dhcp snooping information circuit-id
................................................................................
98
13.8
ip dhcp snooping trust
................................................................................................................
99
13.9
ip dhcp snooping mac-verify
....................................................................................................
99
13.10
ip dhcp snooping limit rate
.....................................................................................................
100
13.11
ip dhcp snooping decline rate
...............................................................................................
101
13.12
show ip source binding
............................................................................................................
102
13.13
show ip dhcp snooping
............................................................................................................
102
13.14
show ip dhcp snooping interface
.........................................................................................
103
13.15
show ip dhcp snooping information interface
.................................................................
103
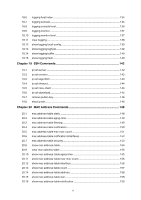
Chapter 14
ARP Inspection Commands
....................................................................
105
14.1
ip arp inspection(global)
..........................................................................................................
105
14.2
ip arp inspection trust
..............................................................................................................
105
14.3
ip arp inspection(interface)
.....................................................................................................
106
14.4
ip arp inspection limit-rate
......................................................................................................
107
14.5
ip arp inspection recover
........................................................................................................
108
14.6
show ip arp inspection
.............................................................................................................
108
V