Fujitsu T4220 T4220 User's Guide - Page 117
reflective material, or interference from external RF sources.
 |
View all Fujitsu T4220 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 117 highlights
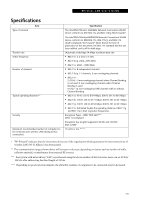
Wireless LAN User's Guide Specifications Item Type of network Transfer rate Active frequency Number of channels Typical operating distances** Security Maximum recommended number of computers to be connected over wireless LAN (during ad hoc connection) Specification The Intel PRO/Wireless 3945ABG Network Connections WLAN device conforms to IEEE 802.11a and 802.11b/g (Wi-Fi based)*. The Intel PRO/Wireless4965ABGN Network Connections WLAN device conforms to IEEE 802.11a, 802.11b/g, and 802.11n (draft-compliant), Wi-Fi based* (Note that at the time of publication of this document, the 802.11n standard had not yet been ratified, and is still in draft stage. (Automatic switching) 54 Mbps maximum data rate ■ 802.11n: 2.4 GHz or 5 GHz ■ 802.11b/g: 2400~2473 MHz ■ 802.11a: 4900 ~ 5850 MHz ■ 802.11a: 8 independent channels ■ 802.11b/g: 11 channels, 3 non-overlapping channels ■ 802.11n: 2.4 GHz - 3 non-overlapping channels when Channel Bonding is not used; 2 non-overlapping channels when Channel Bonding is used. 5 GHz - 12 non-overlapping UNII channels with or without Channel Bonding ■ 802.11a: 40 ft. (12 m) @ 54 Mbps; 300 ft. (91 m) @ 6 Mbps ■ 802.11b: 100 ft. (30 m) @ 11 Mbps; 300 ft. (91 m) @ 1 Mbps ■ 802.11g: 100 ft. (30 m) @ 54 Mbps; 300 ft. (91 m) @ 1 Mbps ■ 802.11n: Estimated double the operating distance of 802.11g and 802.11a in their respective frequencies. Encryption Types - WEP, TKIP, AES*** WPA 1.0 compliant Encryption Key lengths Supported: 64 bits and 128 bits 802.1x/EAP 10 units or less **** * "Wi-Fi based" indicates that the interconnectivity test of the organization which guarantees the interconnectivity of wireless LAN (Wi-Fi Alliance) has been passed. ** The communication ranges shown above will increase or decrease depending on factors such as number of walls, reflective material, or interference from external RF sources. *** Encryption with network key (WEP) is performed using the above number of bits, however, users can set 40 bits/ 104 bits after subtracting the fixed length of 24 bits. **** Depending on practical environments, the allowable number of computers to be connected may be decreased. 109