Brother International 9840CDW Network Users Manual - English - Page 189
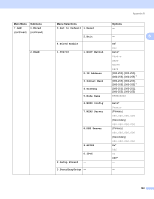
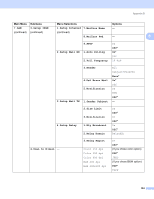
Authentication and encryption for wireless users only, Authentication method, Encryption methods
 |
UPC - 012502618744
View all Brother International 9840CDW manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 189 highlights
Appendix B Authentication and encryption for wireless users only B Authentication method The Brother machine supports the following methods: B B „ Open system Wireless devices are allowed to access the network without any authentication. „ Shared key A secret pre-determined key is shared by all devices that will access the wireless network. The Brother machine uses the WEP keys as the pre-determined key. „ WPA-PSK/WPA2-PSK Enables a Wi-Fi® Protected Access Pre-Shared Key (WPA-PSK), which enables the Brother wireless machine to associate with access points using TKIP for WPA-PSK or AES for WPA-PSK and WPA2-PSK (WPA-Personal). „ LEAP Cisco® LEAP (Light Extensible Authentication Protocol) has been developed by Cisco Systems, Inc. and enables the Brother wireless product to associate with access points using CKIP and CMIC encryptions. Encryption methods B Encryption is used to secure the data that is sent over the wireless network. The Brother machine supports the following encryption methods: „ WEP By using WEP (Wired Equivalent Privacy), the data is transmitted and received with a secure key. „ TKIP TKIP (Temporal Key Integrity Protocol) provides per-packet key mixing a message integrity check and rekeying mechanism. „ AES AES (Advanced Encryption Standard) is Wi-Fi® authorized strong encryption standard. „ CKIP The original Key Integrity Protocol for LEAP by Cisco Systems, Inc. 179