Lexmark MS517 Embedded Web Server--Security: Administrator s Guide - Page 11
Creating a PIN building block for advanced security setup, Setting up internal accounts
 |
View all Lexmark MS517 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 11 highlights
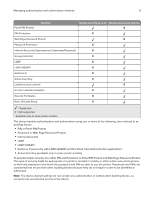
Managing authentication and authorization methods 11 6 If the password is used as the administrator password, then select Admin Password. Note: Functions or settings protected by a user‑level password can be accessed using any administrator‑level password. 7 Click Submit. Notes: • To edit a password, select a password from the list, and then modify the settings. • To delete a password, select a password from the list, and then click Delete Entry. • To delete all passwords in the list, click Delete List. Creating a PIN building block for advanced security setup Note: This feature is available only in advanced‑security devices. PINs are used to control access to specific device menus or to a device itself. PINs can also be required when retrieving a held print, copy, or fax job. 1 From the Embedded Web Server, click Settings > Security > Security Setup. 2 Under Advanced Security Setup, click PIN > Add a PIN. 3 In the Setup Name field, type the name of the PIN configuration. Note: Each PIN must have a unique name containing up to 128 UTF‑8 characters. For example, "Copy Lockout PIN." 4 Type a PIN in the appropriate field, and then retype the PIN to confirm it. 5 If the PIN is used as the Administrator PIN, then click Admin PIN. 6 Click Submit. Changing the PIN length 1 Click Settings > Security > Miscellaneous Security Settings. 2 Enter a number in the Minimum PIN Length field. 3 Click Submit. Setting up internal accounts Note: This feature is available only in advanced‑security devices. Administrators can configure one internal account building block per supported device. Each internal account building block can include a maximum of 750 user accounts and 32 user groups. You can use this building block by itself in a security template to provide authentication‑level security, or with other groups to provide both authentication and authorization.