TP-Link T2600G-52TS TL-SG3452 T2600G-52TS V1 User Guide - Page 224
TP-Link T2600G-52TS TL-SG3452 Manual
 |
View all TP-Link T2600G-52TS TL-SG3452 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 224 highlights
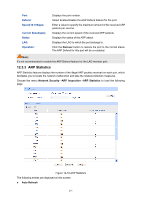
DoS Attack Type Flooding Description the Server. Upon receiving the request packets, the Server responds with SYN-ACK packets. Since the IP address is fake, no response will be returned. The Server will keep on sending SYN-ACK packets. If the attacker sends overflowing fake request packets, the network resource will be occupied maliciously and the requests of the legal clients will be denied. Table 12-1 Defendable DoS Attack Types 12.5.1 DoS Defend On this page, you can enable the DoS Defend type appropriate to your need. Choose the menu Network Security→DoS Defend→DoS Defend to load the following page. Figure 12-18 DoS Defend The following entries are displayed on this screen: Defend Config DoS Defend: Allows you to Enable/Disable DoS Defend function. Defend Table Select: Select the entry to enable the corresponding Defend Type. Defend Type: Displays the Defend Type name. 12.6 802.1X The 802.1X protocol was developed by IEEE802 LAN/WAN committee to deal with the security issues of wireless LANs. It was then used in Ethernet as a common access control mechanism for LAN ports to solve mainly authentication and security problems. 802.1X is a port-based network access control protocol. It authenticates and controls devices requesting for access in terms of the ports of LAN access control devices. With the 802.1X 214