Toshiba Tecra C50 User Guide 2 - Page 122
Bluetooth® wireless technology, Radio Frequency
 |
View all Toshiba Tecra C50 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 122 highlights
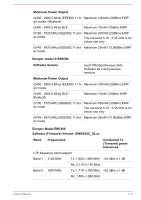
Wireless communication is often subject to local radio regulations. Although Wireless LAN wireless networking products have been designed for operation in the license-free 2.4 GHz and 5 GHz band, local radio regulations might impose a number of limitations to the use of wireless communication equipment. Radio Frequency Band 5 GHz (5150-5850 MHz) (Revision a and n) Band 2.4 GHz (2400-2483.5 MHz) (Revision b/g and n) The range of the wireless signal is related to the transmit rate of the wireless communication. Communications at lower transmit range might travel larger distances. The range of your wireless devices can be affected when the antennas are placed near metal surfaces and solid high-density materials. Range is also impacted due to "obstacles" in the signal path of the radio that might either absorb or reflect the radio signal. Radio Frequency Interference Requirements This device is restricted to indoor use due to its operation in the 5.15 to 5.25GHz frequency range. High-power radars are allocated as primary users (i.e. priority users) of the bands 5.25 to 5.35GHz and 5.65 to 5.85GHz and that these radars could cause interference and/or damage to LE-LAN devices. Bluetooth® wireless technology Some computers in this series have Bluetooth® wireless communication function which eliminates the need for cables between electronic devices such as computers, printers, and mobile phones. When it is enabled, Bluetooth® provides the wireless personal area network environment which is safe and trustworthy, that is quick and easy. You cannot use the built-in Bluetooth® functions of the computer and an external Bluetooth® adaptor simultaneously. For reference, Bluetooth® wireless technology has the following features: Security Two advanced security mechanisms ensure a high level of security: Authentication prevents access to critical data and makes it impossible to falsify the origin of a message. Encryption prevents eavesdropping and maintains link privacy. User's Manual 7-7