HP Visualize J5000 HP Workstations - Graphics Administration Guide For Red Hat - Page 67
XCQUERY-SECURITY-1, GetProperty, There may be multiple <
 |
View all HP Visualize J5000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 67 highlights
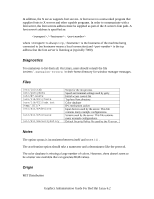
lines are currently ignored. They are intended to specify the site policies used by the XCQUERY-SECURITY-1 authorization method. lines specify how the server should react to untrusted client requests that affect the X Window property named . The rest of this section describes the interpretation of an . For an to apply to a given instance of , must be on a window that is in the set of windows specified by . If is any, the rule applies to on any window. If is root, the rule applies to only on root windows. If is , the following apply. If is a , the rule applies when the window also has that , regardless of its value. If is a , must also have the value specified by . In this case, the property must have type STRING and format 8, and should contain one or more null-terminated strings. If any of the strings match , the rule applies. The definition of string matching is simple case-sensitive string comparison with one elaboration: the occurence of the character '*' in is a wildcard meaning "any string." A can contain multiple wildcards anywhere in the string. For example, "x*" matches strings that begin with x, "*x" matches strings that end with x, "*x*" matches strings containing x, and "x*y*" matches strings that start with x and subsequently contain y. There may be multiple lines for a given . The rules are tested in the order that they appear in the file. The first rule that applies is used. specify operations that untrusted clients may attempt, and the actions that the server should take in response to those operations. can be r (read), w (write), or d (delete). The following table shows how X Protocol property requests map to these operations in The Open Group server implementation. GetProperty ChangeProperty RotateProperties DeleteProperty ListProperties r, or r and d if delete=True w r and w d none, untrusted clients can always list all properti can be "a" (allow), "i" (ignore), or "e" (error). "Allow" means execute the request as if it had been issued by a trusted client. "Ignore" means treat the request as a no-op. In the case of GetProperty, ignore means return an empty property value if the Graphics Administration Guide For Red Hat Linux 6.2