ZyXEL G-300 User Guide - Page 68
Comparison of EAP Authentication Types, Certificate - Server
 |
View all ZyXEL G-300 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 68 highlights
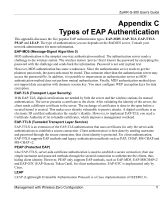
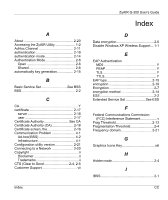
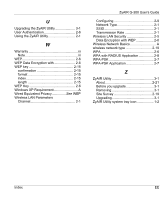
ZyAIR G-300 User's Guide For added security, certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use dynamic keys for data encryption. They are often deployed in corporate environments, but for public deployment, a simple user name and password pair is more practical. The following table is a comparison of the features of five authentication types. Comparison of EAP Authentication Types Mutual Authentication Certificate - Client Certificate - Server Dynamic Key Exchange Credential Integrity Deployment Difficulty Client Identity Protection EAP-MD5 No No No No None Easy No EAP-TLS Yes Yes Yes Yes Strong Hard No EAP-TTLS Yes Optional Yes Yes Strong Moderate Yes PEAP Yes Optional Yes Yes Strong Moderate Yes LEAP Yes No No Yes Moderate Moderate No Z Management with Wireless Zero Configuration