Canon Color imageCLASS X LBP1538C imageCLASS X LBP1538C Users Guide - Page 236
Configuring the IPSec SettingsP. 245, Signature Algorithm]
 |
View all Canon Color imageCLASS X LBP1538C manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 236 highlights
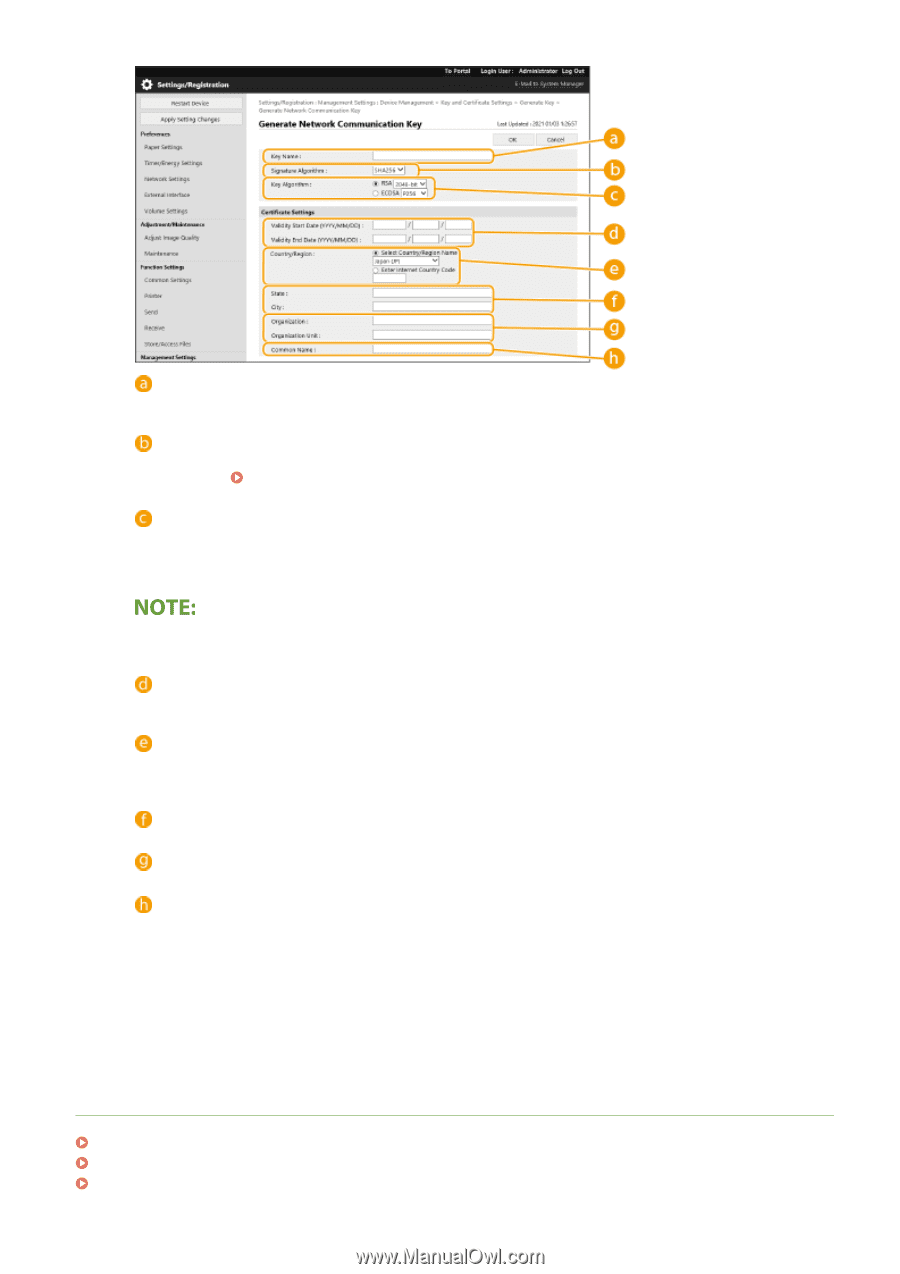
Managing the Machine [ Key Name] Enter alphanumeric characters for naming the key. Set a name that will be easy for you to find later in a list. [Signature Algorithm] Select the hash algorithm to use for the signature. The available hash algorithms vary depending on the key length ( Management Functions(P. 525) ). A key length of 1024 bits or more can support SHA384 and SHA512 hash algorithms. [Key Algorithm] Select [RSA] or [ECDSA] as the key generation algorithm. Select the key length if you selected [RSA] and the key type if you selected [ECDSA]. In both cases, a higher value provides greater security but reduces the communication processing speed. ● If [SHA384] or [SHA512] is selected for [Signature Algorithm], the key length cannot be set to [512-bit] when [RSA] is selected for [Key Algorithm]. [ Validity Start Date (YYYY/MM/DD)]/[Validity End Date (YYYY/MM/DD)] Enter the start date and end date of the validity period for the certificate. [Validity End Date (YYYY/MM/ DD)] cannot be set to a date before the date in [Validity Start Date (YYYY/MM/DD)]. [Country/Region] Click the [Select Country/Region] radio button and select the country/region from the drop-down list. You can also click the [Enter Internet Country Code] radio button and enter a country code, such as "US" for the United States. [State]/[City] Enter alphanumeric characters for the location as necessary. [Organization]/[Organization Unit] Enter alphanumeric characters for the organization name as necessary. [Common Name] Enter alphanumeric characters for the common name of the certificate as necessary. "Common Name" is often abbreviated as "CN." 7 Click [OK]. ● Generating a key and certificate may take some time. ● After the key and certificate is generated, it is automatically registered to the machine. LINKS Registering a Key and Certificate for Network Communication(P. 233) Configuring the Key and Certificate for TLS(P. 224) Configuring the IPSec Settings(P. 245) 229