Canon Color imageCLASS X LBP1538C imageCLASS X LBP1538C Users Guide - Page 534
Registration of Certificate Revocation Lists CRL, Definition of Weak Encryption
 |
View all Canon Color imageCLASS X LBP1538C manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 534 highlights
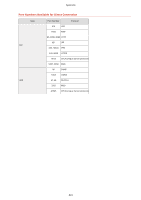
Appendix ◼ Registration of Certificate Revocation Lists (CRL) Up to 50 certificate revocation lists (CRL) can be registered. Note, however, that CRL cannot be registered in the following cases. ● The data size of the CRL exceeds 1 MB. ● An unsupported signature algorithm is being used. ● The number of revoked certificates registered in one CRL file exceeds 1,000. ◼ Definition of "Weak Encryption" When [Prohibit Use of Weak Encryption] is selected, the use of the following algorithms is prohibited. Hash: MD4, MD5, SHA-1 HMAC: HMAC-MD5 Common key cryptosystem: RC2, RC4, DES Public key cryptosystem: RSA encryption (512 bits/1024 bits), RSA signature (512 bits/1024 bits), DSA (512 bits/1024 bits), DH (512 bits/1024 bits) ● Even when [Prohibit Use of Key/Certificate with Weak Encryption] is selected, the hash algorithm SHA-1, which is used for signing a root certificate, can be used. ◼ FIPS 140-2 Standard Algorithm When [Format Encryption Method to FIPS 140-2] is selected, the following algorithms are prohibited from use. Hash: MD4, MD5, SHA-1 (for a purpose other than TLS) Common key cryptosystem: RC2, RC4, DES, PBE Public key cryptosystem: RSA encryption (512 bits/1024 bits), RSA signature (512 bits/1024 bits), DSA signature (512 bits/1024 bits), DH (512 bits/1024 bits) ◼ Log Management ● The following types of logs can be managed on the machine. Collected logs can be exported in the CSV file format. Log Type Number Indicated as "Log Type" in the CSV File Description User Authentication Log 4098 This log contains information related to the authentication status of user authentication (login/logout and user authentication success/failure), the registering/changing/ 527