Dell G5 5090 Service Manual - Page 67
System and setup password
 |
View all Dell G5 5090 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 67 highlights
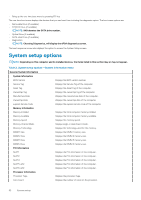
Table 9. System setup options-Virtualization Support menu Virtualization Support Virtualization Specify whether a Virtual Machine Monitor (VMM) can utilize the additional hardware capabilities provided by Intel Virtualization Technology. VT for Direct I/O Specify whether a Virtual Machine Monitor (VMM) can utilize the additional hardware capabilities provided by Intel Virtualization Technology for Direct I/O. Trusted Execution Enable or disable trusted execution. Table 10. System setup options-Wireless menu Wireless Wireless Device Enable Enable or disable internal wireless devices. Table 11. System setup options-Maintenance menu Maintenance Service Tag Display the system's Service Tag. Asset Tag Create a system Asset Tag. SERR Messages Enable or disable SERR messages. Dell development configuration Enable or disable Dell development configuration. BIOS Downgrade Control flashing of the system firmware to previous revisions. Data Wipe Enable to securely erase data from all internal storage devices. BIOS Recovery Enable the user to recover from certain corrupted BIOS conditions from a recovery file on the user primary hard drive or an external USB key. Table 12. System setup options-System Logs menu System Logs BIOS Events Display BIOS events. Table 13. System setup options-SupportAssist System Resolution menu SupportAssist System Resolution Auto OS Recovery Threshold Control the automatic boot flow for SupportAssist System Resolution Console and for Dell OS Recovery tool. System and setup password Table 14. System and setup password Password type System password Setup password Description Password that you must enter to log on to your system. Password that you must enter to access and make changes to the BIOS settings of your computer. You can create a system password and a setup password to secure your computer. CAUTION: The password features provide a basic level of security for the data on your computer. CAUTION: Anyone can access the data stored on your computer if it is not locked and left unattended. NOTE: System and setup password feature is disabled. System setup 67