HP 6120XG HP ProCurve Series 6120 Blade Switches Access Security Guide - Page 23
Security Overview, Contents
 |
View all HP 6120XG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 23 highlights
Security Overview Security Overview Contents 1 Contents Introduction 1-2 About This Guide 1-2 For More Information 1-2 Access Security Features 1-3 Network Security Features 1-7 Getting Started with Access Security 1-9 Physical Security 1-9 Quick Start: Using the Management Interface Wizard 1-10 CLI: Management Interface Wizard 1-10 Web: Management Interface Wizard 1-12 SNMP Security Guidelines 1-15 Precedence of Security Options 1-17 Precedence of Port-Based Security Options 1-17 Precedence of Client-Based Authentication: Dynamic Configuration Arbiter 1-17 Network Immunity Manager 1-18 Arbitrating Client-Specific Attributes 1-19 ProCurve Identity-Driven Manager (IDM 1-21 1-1

1-1
Security Overview
Contents
1
Security Overview
Contents
Introduction
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2
About This Guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2
For More Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2
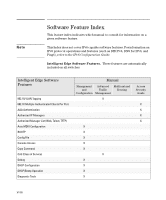
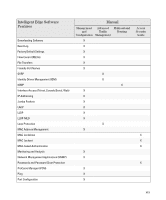
Access Security Features
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3
Network Security Features
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-7
Getting Started with Access Security
. . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9
Physical Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9
Quick Start: Using the Management Interface Wizard . . . . . . . . . . . . 1-10
CLI: Management Interface Wizard . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Web: Management Interface Wizard
. . . . . . . . . . . . . . . . . . . . . . . 1-12
SNMP Security Guidelines . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-15
Precedence of Security Options
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-17
Precedence of Port-Based Security Options
. . . . . . . . . . . . . . . . . . . . 1-17
Precedence of Client-Based Authentication:
Dynamic Configuration Arbiter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-17
Network Immunity Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-18
Arbitrating Client-Specific Attributes
. . . . . . . . . . . . . . . . . . . . . . 1-19
ProCurve Identity-Driven Manager (IDM)
. . . . . . . . . . . . . . . . . . . . . 1-21