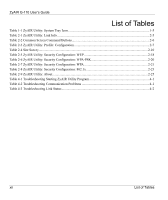
ZyAIR G-110 User’s Guide
x
Table of Contents
2.8.2
Authentication Mode
.........................................................................................................
2-13
2.8.3
IEEE 802.1x
.......................................................................................................................
2-13
2.8.4
WPA
..................................................................................................................................
2-13
2.8.5
WPA-PSK Application Example
.......................................................................................
2-14
2.8.6
WPA with RADIUS Application Example
........................................................................
2-15
2.9
Configuring Wireless Security on the ZyAIR
.............................................................................
2-16
2.9.1
WEP Encryption
................................................................................................................
2-17
2.9.2
WPA-PSK
..........................................................................................................................
2-19
2.9.3
WPA
..................................................................................................................................
2-20
2.9.4
IEEE802.1x
........................................................................................................................
2-22
2.10
The About Screen
.......................................................................................................................
2-24
Chapter 3 Maintenance
.............................................................................................................................
3-1
3.1
Uninstalling the ZyAIR Utility
.....................................................................................................
3-1
3.2
Upgrading the ZyAIR Utility
........................................................................................................
3-1
Chapter 4 Troubleshooting
.......................................................................................................................
4-1
4.1
Problems Starting the ZyAIR Utility Program
.............................................................................
4-1
4.2
Problems Communicating With Other Computers
.......................................................................
4-1
4.3
Problem with the Link Status
.......................................................................................................
4-2
Appendix A Types of EAP Authentication
................................................................................................
A
Appendix B Product Specifications
............................................................................................................
C
Index
..............................................................................................................................................................
F