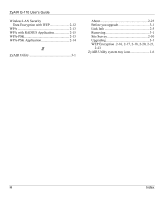
ZyAIR G-110 User’s Guide
Index
G
N
Network Configuration Profile
.......................
2-9
Deleting
.....................................................
2-10
Saving
.........................................................
2-9
Using a pre-configured profile
..................
2-10
Network Type
.................................................
2-2
Ad-Hoc(IBSS)
.............................................
2-2
Infrastructure
...............................................
2-2
O
Online Registration
...........................................
iii
Open authentication mode
.............................
2-13
Operating Mode
.....................
See
Network Type
P
passphrase
.....................................................
2-12
PEAP
.................................................................
A
Preface
............................................................
xiii
problem description
.........................................
4-1
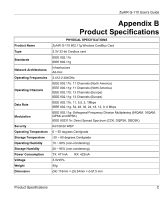
Product specifications
.......................................
C
Profile
..............................................................
2-9
Network Configuration
...............................
2-9
Protected EAP
......................................
See
PEAP
R
Related Documentation
...................................
xiii
Roaming
..........................................................
2-3
Example
......................................................
2-4
S
Service Set Identity
...............................
See
SSID
Shared authentication mode
..........................
2-13
Site Survey
....................................................
2-10
SSID
........................................................
2-1, 2-7
Syntax Conventions
........................................
xiii
T
Temporal Key Integrity Protocol
..................
2-14
TKIP
..........
See
Temporal Key Integrity Protocol
TLS
...................................................................
A
Transmission rate
............................................
2-1
Transport Layer Security
........................
See TLS
Troubleshooting
..............................................
4-1
Checking Hardware Conflict
.......................
4-1
Communication problems
...........................
4-1
Radio interference
.......................................
4-2
Site Survery
.................................................
4-2
Starting ZyAIR Utility
................................
4-1
TTLS
.................................................................
A
Tunneled Transport Layer Service
.......
See
TTLS
U
Upgrading the ZyAIR Utility
..........................
3-1
User Authentication
......................................
2-13
Using the ZyAIR Utility
..................................
2-1
V
Viewing Current Configuration
......................
2-4
W
Warranty
............................................................
iii
Note
...............................................................
iii
WEP
..............................................................
2-12
WEP Data Encryption
Configuring
...............................................
2-16
WEP Data Encryption with
...........................
2-12
WEP Key
.......................................................
2-12
Wired Equivalent Privacy
.....................
See
WEP
Wireless LAN Parameters
Channel
.......................................................
2-1
Configuring
.................................................
2-6
Network Type
..............................................
2-2
SSID
............................................................
2-1
Transmission Rate
.......................................
2-1