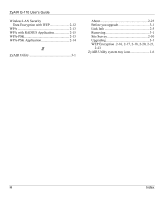
ZyAIR G-110 User’s Guide
F
Index
Index
A
About
............................................................
2-24
Accessing the ZyAIR Utility
..........................
1-5
Authentication Mode
....................................
2-13
Open
..........................................................
2-13
Shared
.......................................................
2-13
Automatic WEP key generation
....................
2-12
B
Basic Service Set
....................................
See
BSS
BSS
.................................................................
2-2
C
CA
.....................................................................
A
Certificate Authority
................................
See
CA
Channel
...........................................................
2-8
Common Screen Command Buttons
...............
2-6
Communication Problem
................................
4-1
Ad-hoc(IBSS)
.............................................
4-2
Infrastructure
...............................................
4-2
Connecting to a Network
..............................
2-11
Copyright
...........................................................
ii
Disclaimer
......................................................
ii
Trademarks
....................................................
ii
Create WEP key with passphrase ...2-19, 2-20, 2-
21, 2-23
Customer Support
............................................
vii
D
Data encryption
.............................................
2-12
Disable Windows XP Wireless Support
.........
1-1
E
EAP Authentication
MD5
..............................................................
A
PEAP
.............................................................
A
TLS
...............................................................
A
TTLS
.............................................................
A
Encryption
.....................................................
2-14
ESS
.................................................................
2-3
Extended Service Set
..............................
See
ESS
F
Federal Communications Commission (FCC)
Interference Statement
...................................
v
G
Graphics Icons Key
.........................................
xiv
I
IBSS
................................................................
2-2
IEEE 802.11g
..................................................
1-1
Independent Basic Service Set
..............
See
IBSS
Information for Canadian Users
........................
iv
Caution
..........................................................
iv
Note
...............................................................
iv
Infrastructure
...................................................
2-2
L
Link Info
.........................................................
2-4
M
MD5
..................................................................
A
Message Digest Algorithm 5
................
See
MD5
Message Integrity Check
...............................
2-14
MIC
........................
See
Message Integrity Check