McAfee MEJCAE-AM-DA Product Guide - Page 11
Basic steps for using E-Business Server, public key, private key, plaintext, ciphertext, decryption
 |
View all McAfee MEJCAE-AM-DA manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 11 highlights
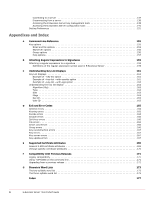
E-Business Server Basics Basic steps for using E-Business Server Figure 2-1 Public Key Cryptography diagram public key private key plaintext encryption decryption ciphertext plaintext For a comprehensive overview of encryption technology, refer to "An Introduction to Cryptography." Basic steps for using E-Business Server This section takes a quick look at the procedures a user would normally follow in the course of using E-Business Server. For details concerning any of these procedures, refer to the appropriate chapters in this book. The order in which you perform the following tasks will vary. 1 Install E-Business Server on your server. You will find detailed installation instructions in an accompanying Installation Guide or ReadMe file. 2 Configure E-Business Server to meet your needs. You can configure E-Business Server to perform in a specific way. For example, you can specify what encryption and hash algorithms E-Business Server should use, tell E-Business Server to add a specific comment to everything you encrypt, always encrypt a copy of your data to your own key as well as your recipient's, set the level of skepticism E-Business Server should use in determining whether others' keys are valid, and so on. You do this by setting values in E-Business Server's configuration files as described in Using the Configuration File on page 86 3 Create a private and public key pair. To use E-Business Server, you need a key pair. A key pair, as described in the section "'Key' concepts," above, is composed of a private key to which only you have access and a public key that you can copy and make freely available to everyone with whom you exchange information. You can create a new key pair any time after you have finished the E-Business Server installation procedure. For more information about creating a private and public key pair, refer to Creating a key pair on page 18. 4 Exchange public keys with others (optional). 9 E-Business Server™ 8.6 Product Guide