Dell Brocade G620 Brocade 8.0.1 Fabric OS Administratiors Guide - Page 160
Remote authentication, Remote authentication configuration, Client/server model
 |
View all Dell Brocade G620 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 160 highlights
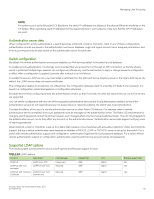
Managing User Accounts 3. Create a serial connection to the standby CP blade as described in Connecting to Fabric OS through the serial port on page 38. 4. Reboot the standby CP blade by sliding the On/Off switch on the ejector handle of the standby CP blade to Off , and then back to On . This causes the blade to reset. 5. Press Esc within four seconds after the message "Press escape within 4 seconds..."is displayed. 6. When prompted, enter 3 to enter the command shell. 7. Enter the passwd command at the shell prompt. The passwd command applies only to the boot PROM password when it is entered from the boot interface. 8. Enter the boot PROM password at the prompt, and then re-enter it when prompted. The password must be eight alphanumeric characters long (any additional characters are not recorded). Record this password for future use. 9. Enter the saveEnv command to save the new password. 10. Reboot the standby CP blade by entering the reset command. 11. Connect to the active CP blade over a serial or Telnet connection and enter the haEnable command to restore high availability, and then fail over the active CP blade by entering the haFailover command. Traffic resumes flowing through the newly active CP blade after it has completed rebooting. 12. Connect the serial cable to the serial port on the new standby CP blade (previously the active CP blade). 13. Repeat step 3 through step 10 for the new standby CP blade. 14. Connect to the active CP blade over a serial or Telnet connection and enter the haEnable command to restore high availability. NOTE To recover lost passwords, refer to the Fabric OS Troubleshooting and Diagnostics Guide. Remote authentication Fabric OS supports user authentication through the local user database or one of the following external authentication services: ∙ Remote authentication dial-in user service (RADIUS) ∙ Lightweight Directory Access Protocol (LDAP) using Microsoft Active Directory in Windows or OpenLDAP in Linux. ∙ LDAP is supported with Windows 2008-2012 running LDAP 2003-2008 schema. ∙ Terminal Access Controller Access-Control System Plus (TACACS+) Remote authentication configuration A switch can be configured to try one of the supported remote authentication services (RADIUS, LDAP, or TACACS+) and local switch authentication. The switch can also be configured to use only a remote authentication service, or only local switch authentication. Client/server model When configured to use one of the supported remote authentication services, the switch acts as a Network Access Server (NAS) and RADIUS, LDAP, or TACACS+ client. The switch sends all authentication, authorization, and accounting (AAA) service requests to the authentication server. The authentication server receives the request, validates the request, and sends its response back to the switch. The supported management access channels that integrate with RADIUS, LDAP, and TACACS+ include serial port, Telnet, SSH, and Web Tools. All these access channels require the switch IP address or name to connect. RADIUS, LDAP, and TACACS+ servers accept both IPv4 and IPv6 address formats. For accessing both the active and standby CP blades, and for the purpose of HA failover, both CP IP addresses of a Backbone should be included in the authentication server configuration. Brocade Fabric OS Administration Guide, 8.0.1 160 53-1004111-02