Netgear WG511U WG511U User Manual - Page 69
Key management, Data Privacy Encryption, Data integrity
 |
UPC - 606449037333
View all Netgear WG511U manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 69 highlights
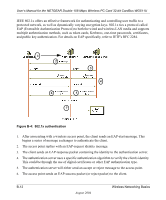
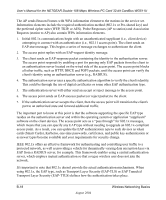
User's Manual for the NETGEAR Double 108 Mbps Wireless PC Card 32-bit CardBus WG511U The supplicant in the station uses the authentication and cipher suite information contained in the information elements to decide which authentication method and cipher suite to use. For example, if the access point is using the Pre-shared key method then the supplicant need not authenticate using full-blown 802.1X. Rather, the supplicant must simply prove to the access point that it is in possession of the pre-shared key. If the supplicant detects that the service set does not contain a WPA information element then it knows it must use pre-WPA 802.1X authentication and key management in order to access the network. • Key management. WPA features a robust key generation/management system that integrates the authentication and data privacy functions. Keys are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Temporal Key Integrity Protocol (TKIP) is used to wrap WEP in sophisticated cryptographic and security techniques to overcome most of its weaknesses. • Data integrity. TKIP includes a message integrity code (MIC) at the end of each plaintext message to ensure messages are not being spoofed. Client with a WPA-enabled wireless adapter and supplicant For example, a WPA-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure B-6: WPA/802.1x Authentication Sequence Wireless Networking Basics August 2004 B-17