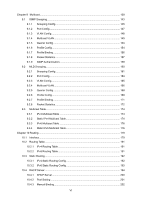
13.2.2
ACL Create
......................................................................................................
240
13.2.3
MAC ACL
.........................................................................................................
240
13.2.4
Standard-IP ACL
..............................................................................................
242
13.2.5
Extend-IP ACL
.................................................................................................
243
13.2.6
Combined ACL
................................................................................................
244
13.2.7
IPv6 ACL
..........................................................................................................
245
13.3
Policy Config
..............................................................................................................
247
13.3.1
Policy Summary
..............................................................................................
247
13.3.2
Policy Create
...................................................................................................
248
13.3.3
Action Create
...................................................................................................
248
13.4
ACL Binding
................................................................................................................
249
13.4.1
Binding Table
...................................................................................................
250
13.4.2
Port Binding
.....................................................................................................
251
13.4.3
VLAN Binding
..................................................................................................
252
13.5
Policy Binding
.............................................................................................................
252
13.5.1
Binding Table
...................................................................................................
253
13.5.2
Port Binding
.....................................................................................................
254
13.5.3
VLAN Binding
..................................................................................................
255
13.6
Application Example for ACL
......................................................................................
255
Chapter 14
Network Security
........................................................................................................
258
14.1
IP-MAC Binding
..........................................................................................................
258
14.1.1
Binding Table
...................................................................................................
258
14.1.2
Manual Binding
................................................................................................
259
14.1.3
ARP Scanning
.................................................................................................
261
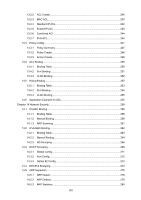
14.2
IPv6-MAC Binding
......................................................................................................
262
14.2.1
Binding Table
...................................................................................................
263
14.2.2
Manual Binding
................................................................................................
264
14.2.3
ND Snooping
...................................................................................................
266
14.3
DHCP Snooping
.........................................................................................................
268
14.3.1
Global Config
...................................................................................................
271
14.3.2
Port Config
.......................................................................................................
272
14.3.3
Option 82 Config
.............................................................................................
273
14.4
DHCPv6 Snooping
.....................................................................................................
274
14.5
ARP Inspection
...........................................................................................................
275
14.5.1
ARP Detect
......................................................................................................
278
14.5.2
ARP Defend
.....................................................................................................
279
14.5.3
ARP Statistics
..................................................................................................
280
VIII