ZyXEL P-2802HWL-I1 User Guide - Page 371
Security Parameters Summary
 |
View all ZyXEL P-2802HWL-I1 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 371 highlights
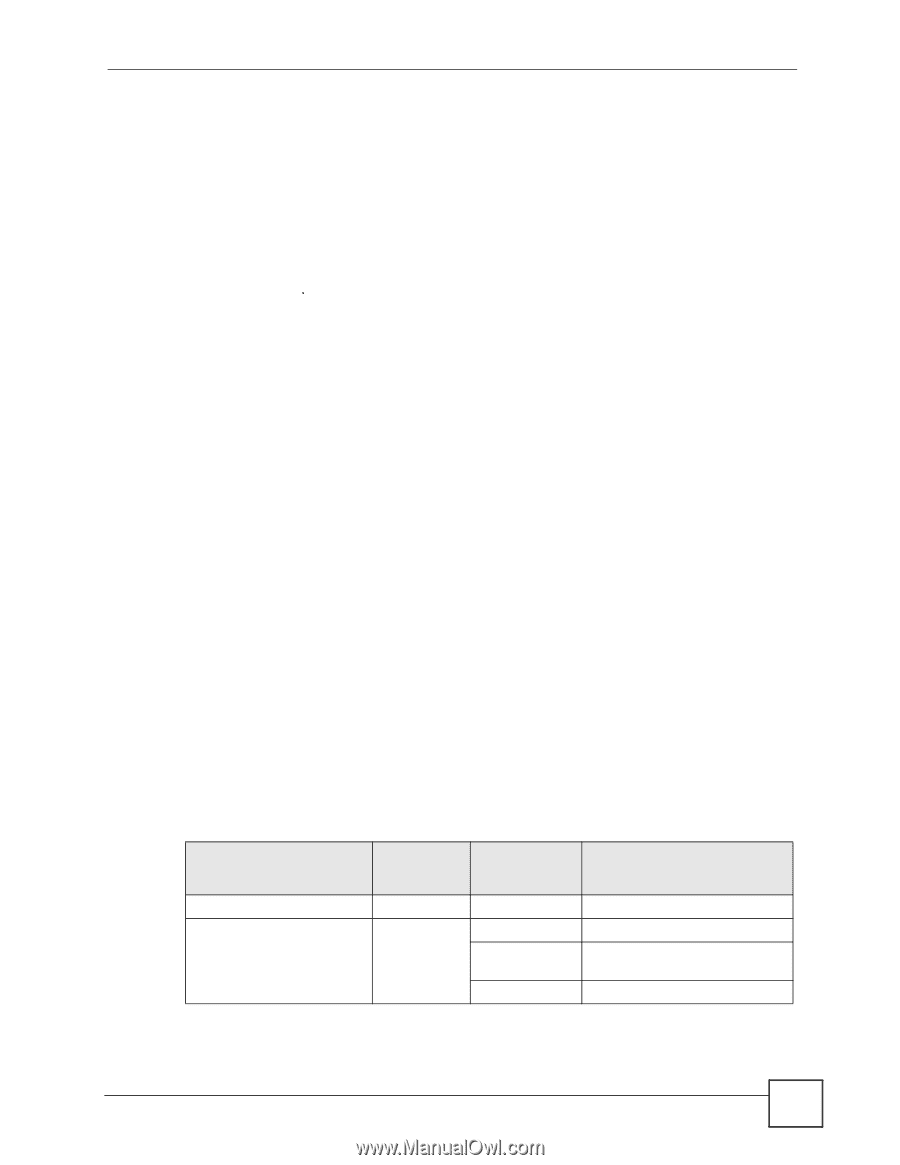
Appendix D Wireless LANs Encryption WPA improves data encryption by using Temporal Key Integrity Protocol (TKIP) or Advanced Encryption Standard (AES), Message Integrity Check (MIC) and IEEE 802.1x. TKIP uses 128-bit keys that are dynamically generated and distributed by the authentication server. It includes a per-packet key mixing function, a Message Integrity Check (MIC) named Michael, an extended initialization vector (IV) with sequencing rules, and a re-keying mechanism. TKIP regularly changes and rotates the encryption keys so that the same encryption key is never used twice. The RADIUS server distributes a Pairwise Master Key (PMK) key to the AP that then sets up a key hierarchy and management system, using the PMK to dynamically generate unique data encryption keys to encrypt every data packet that is wirelessly communicated between the AP and the wireless stations. This all happens in the background automatically. AES (Advanced Encryption Standard) also uses a secret key. This implementation of AES applies a 128-bit key to 128-bit blocks of data. The Message Integrity Check (MIC) is designed to prevent an attacker from capturing data packets, altering them and resending them. The MIC provides a strong mathematical function in which the receiver and the transmitter each compute and then compare the MIC. If they do not match, it is assumed that the data has been tampered with and the packet is dropped. By generating unique data encryption keys for every data packet and by creating an integrity checking mechanism (MIC), TKIP makes it much more difficult to decrypt data on a Wi-Fi network than WEP, making it difficult for an intruder to break into the network. The encryption mechanisms used for WPA and WPA-PSK are the same. The only difference between the two is that WPA-PSK uses a simple common password, instead of user-specific credentials. The common-password approach makes WPA-PSK susceptible to brute-force password-guessing attacks but it's still an improvement over WEP as it employs an easier-touse, consistent, single, alphanumeric password. Security Parameters Summary Refer to this table to see what other security parameters you should configure for each Authentication Method/ key management protocol type. MAC address filters are not dependent on how you configure these security features. Table 166 Wireless Security Relational Matrix AUTHENTICATION METHOD/ KEY MANAGEMENT PROTOCOL ENCRYPTIO N METHOD ENTER MANUAL KEY ENABLE IEEE 802.1X Open None No No Open WEP No Enable with Dynamic WEP Key Yes Enable without Dynamic WEP Key Yes Disable P-2802H(W)(L)-I Series User's Guide 371