TP-Link TL-R600VPN TL-R600VPN V1 User Guide - Page 52
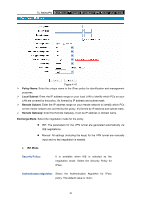
Policy Name, Local Subnet, Remote Subnet, Remote Gateway, Exchange Mode, IKE Mode
 |
View all TP-Link TL-R600VPN manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 52 highlights
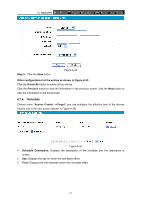
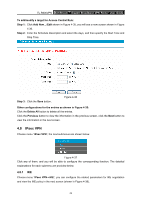
TL-R600VPN SafeStreamTM Gigabit Broadband VPN Router User Guide Figure 4-41 ¾ Policy Name: Enter the unique name to the IPsec policy for identification and management purposes. ¾ Local Subnet: Enter the IP address range on your local LAN to identify which PCs on your LAN are covered by this policy. It's formed by IP address and subnet mask. ¾ Remote Subnet: Enter the IP address range on your remote network to identify which PCs on the remote network are covered by this policy. It's formed by IP address and subnet mask. ¾ Remote Gateway: Enter the Remote Gateway. It can be IP address or domain name. Exchange Mode: Select the negotiation mode for the policy. z IKE: The parameters for the VPN tunnel are generated automatically via IKE negotiations. z Manual: All settings (including the keys) for the VPN tunnel are manually input and no key negotiation is needed. z IKE Mode Security Policy: It is available when IKE is selected as the negotiation mode. Select the Security Policy for IPsec. Authentication Algorithm: Select the Authentication Algorithm for IPsec policy. The default value is "Auto". 46