Cisco CISCO876-SEC-I-K9 Configuration Guide - Page 75
Apply the Crypto Map to the Physical Interface
 |
UPC - 882658021800
View all Cisco CISCO876-SEC-I-K9 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 75 highlights
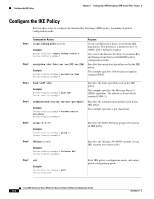
Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Apply the Crypto Map to the Physical Interface Step 3 Command or Action reverse-route Example: Router(config-crypto-map)# reverse-route Router(config-crypto-map)# Purpose Creates source proxy information for the crypto map entry. See the Cisco IOS Security Command Reference for details. Step 4 exit Returns to global configuration mode. Example: Router(config-crypto-map)# exit Router(config)# Step 5 crypto map map-name seq-num [ipsec-isakmp] Creates a crypto map profile. [dynamic dynamic-map-name] [discover] [profile profile-name] Example: Router(config)# crypto map static-map 1 ipsec-isakmp dynamic dynmap Router(config)# Apply the Crypto Map to the Physical Interface The crypto maps must be applied to each interface through which IP Security (IPSec) traffic flows. Applying the crypto map to the physical interface instructs the router to evaluate all the traffic against the security associations database. With the default configurations, the router provides secure connectivity by encrypting the traffic sent between remote sites. However, the public interface still allows the rest of the traffic to pass and provides connectivity to the Internet. Perform these steps to apply a crypto map to an interface, beginning in global configuration mode: Step 1 Command or Action interface type number Example: Router(config)# interface fastethernet 4 Router(config-if)# Purpose Enters the interface configuration mode for the interface to which you want the crypto map applied. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-9