Linksys WAG54G User Guide - Page 33
The Security Tab, Enabled, Disabled, Block Anonymous Internet Requests, View Logs, Save Settings
 |
View all Linksys WAG54G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 33 highlights
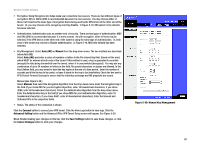
Wireless-G ADSL Gateway The Security Tab Firewall When you click the Security tab, you will see the Firewall screen (see Figure 5-18). This screen contains Filters and the option to Block WAN Requests. Filters block specific Internet data types and block anonymous Internet requests. • Firewall. To add Firewall Protection, click Enabled. If you do not want Firewall Protection, click Disabled. Additional Filters • Filter Proxy. Use of WAN proxy servers may compromise the Gateway's security. Denying Filter Proxy will disable access to any WAN proxy servers. To enable proxy filtering, click Enabled. • Filter Cookies. A cookie is data stored on your computer and used by Internet sites when you interact with them. To enable cookie filtering, click Enabled. • Filter Java Applets. Java is a programming language for websites. If you deny Java Applets, you run the risk of not having access to Internet sites created using this programming language. To enable Java Applet filtering, click Enabled. • Filter ActiveX. ActiveX is a programming language for websites. If you deny ActiveX, you run the risk of not having access to Internet sites created using this programming language. To enable ActiveX filtering, click Enabled. Block WAN requests • Block Anonymous Internet Requests. This keeps your network from being "pinged" or detected and reinforces your network security by hiding your network ports, so it is more difficult for intruders to discover your network. Select Block Anonymous Internet Requests to block anonymous Internet requests or deselect it to allow anonymous Internet requests. Click View Logs to view a log of any firewall events. When finished making your changes on this tab, click the Save Settings button to save these changes, or click the Cancel Changes button to undo your changes. Chapter 5: Configuring the Gateway The Security Tab Figure 5-18: Firewall 26