Netgear FVS114NA FVS114 Reference Manual - Page 102
Certificate Revocation List (CRL), Walk-Through of Configuration Scenarios on the FVS114
 |
View all Netgear FVS114NA manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 102 highlights
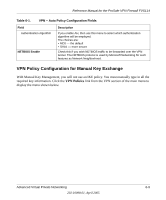
Reference Manual for the ProSafe VPN Firewall FVS114 Each CA has its own certificate. The certificates of a CA are added to the FVS114 and then can be used to form IKE policies for the user. Once a CA certificate is added to the FVS114 and a certificate is created for a user, the corresponding IKE policy is added to the FVS114. Whenever the user tries to send traffic through the FVS114, the certificates are used in place of pre-shared keys during initial key exchange as the authentication and key generation mechanism. Once the keys are established and the tunnel is set up the connection proceeds according to the VPN policy. Certificate Revocation List (CRL) Each Certification Authority (CA) maintains a list of the revoked certificates. The list of these revoked certificates is known as the Certificate Revocation List (CRL). Whenever an IKE policy receives the certificate from a peer, it checks for this certificate in the CRL on the FVS114 obtained from the corresponding CA. If the certificate is not present in the CRL it means that the certificate is not revoked. IKE can then use this certificate for authentication. If the certificate is present in the CRL it means that the certificate is revoked, and the IKE will not authenticate the client. You must manually update the FVS114 CRL regularly in order for the CA-based authentication process to remain valid. Walk-Through of Configuration Scenarios on the FVS114 There are a variety of configurations you might implement with the FVS114. The scenarios listed below illustrate typical configurations you might use in your organization. In order to help make it easier to set up an IPsec system, the following two scenarios are provided. These scenarios were developed by the VPN Consortium (http://www.vpnc.org). The goal is to make it easier to get the systems from different vendors to interoperate. NETGEAR is providing you with both of these scenarios in the following two formats: • VPN Consortium Scenarios without any product implementation details • VPN Consortium Scenarios based on the FVS114 User Interface The purpose of providing these two versions of the same scenarios is to help you determine where the two vendors use different vocabulary. Seeing the examples presented in these different ways will reveal how systems from different vendors do the same thing. 6-14 Advanced Virtual Private Networking 202-10098-01, April 2005