Cisco DS-C9124-K9 Troubleshooting Guide - Page 341
User Cannot Access Certain Features, Troubleshooting RADIUS and TACACS+ With Cisco ACS
 |
View all Cisco DS-C9124-K9 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 341 highlights
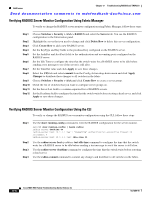
Chapter 17 Troubleshooting RADIUS and TACACS+ Troubleshooting RADIUS and TACACS+ With Cisco ACS Send documentation comments to [email protected] User Cannot Access Certain Features Symptom User cannot access certain features. Table 17-4 User Cannot Access Certain Features Symptom User cannot access certain features. Possible Cause User is assigned incorrect role. Solution For RADIUS, configure the vendor-specific attributes on the server for the role using: Cisco-AVPair = shell:roles="rolename1 rolename2". Role is not configured for appropriate access. For TACACS+, configure the attribute/value pair on the server for the role using: roles="rolename1 rolename2". Verify that all roles are defined on the switch. See Chapter 18, "Troubleshooting Users and Roles." Troubleshooting RADIUS and TACACS+ With Cisco ACS To troubleshoot RADIUS and TACACS+ issues with Cisco ACS, follow these steps: Step 1 Step 2 Step 3 Choose Network Configuration using Cisco ACS and view the AAA Clients table to verify that the Cisco SAN-OS switch is configured as an AAA client on Cisco ACS. Choose User Setup > User Data Configuration to verify that the user is configured. View the Cisco IOS/PIX RADIUS Attributes setting for a user. Verify that the user is assigned the correct roles in the AV-pairs. For example, shell:roles="network-admin". Note The Cisco IOS/PIX RADIUS Attributes field is case-sensitive. Verify that the role listed in the AV-pair exists on the Cisco SAN-OS switch. Step 4 Step 5 Step 6 Step 7 If the Cisco IOS/PIX RADIUS Attributes field is not present, follow these steps: a. Choose Interface > RADIUS (Cisco IOS/PIX). b. Check the User and Group check boxes for the cisco-av-pair option and click Submit. c. Choose User Setup > User Data Configuration and add the AV-pair to assign the correct role to each user. Choose System Configuration > Logging to activate logs to look for reasons for failed authentication attempts. Choose Reports and Activity to view the resulting logs. On the Cisco SAN-OS switch, use the show radius-server command to verify that the RADIUS server timeout value is set to 5 seconds or greater. OL-9285-05 Cisco MDS 9000 Family Troubleshooting Guide, Release 3.x 17-11