ZyXEL NWA1123-NI User Guide - Page 198
Security Parameters Summary, Table 58, AUTHENTICATION, METHOD/ KEY, MANAGEMENT PROTOCOL
 |
View all ZyXEL NWA1123-NI manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 198 highlights
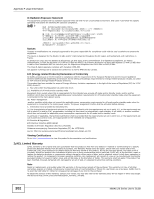
Appendix E Wireless LANs 1 First enter identical passwords into the AP and all wireless clients. The Pre-Shared Key (PSK) must consist of between 8 and 63 ASCII characters or 64 hexadecimal characters (including spaces and symbols). 2 The AP checks each wireless client's password and allows it to join the network only if the password matches. 3 The AP and wireless clients generate a common PMK (Pairwise Master Key). The key itself is not sent over the network, but is derived from the PSK and the SSID. 4 The AP and wireless clients use the TKIP or AES encryption process, the PMK and information exchanged in a handshake to create temporal encryption keys. They use these keys to encrypt data exchanged between them. Figure 96 WPA(2)-PSK Authentication Security Parameters Summary Refer to this table to see what other security parameters you should configure for each authentication method or key management protocol type. MAC address filters are not dependent on how you configure these security features. Table 58 Wireless Security Relational Matrix AUTHENTICATION METHOD/ KEY MANAGEMENT PROTOCOL ENCRYPTIO N METHOD ENTER MANUAL KEY Open None No Open Shared WPA WPA-PSK WEP No Yes Yes WEP No Yes Yes TKIP/AES No TKIP/AES Yes IEEE 802.1X Disable Enable without Dynamic WEP Key Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable Disable 198 NWA1120 Series User's Guide