ZyXEL Vantage Report 2.3 User Guide - Page 30
ZyNOS-based ZyWALL Configuration Requirements by Menu Item
 |
View all ZyXEL Vantage Report 2.3 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 30 highlights
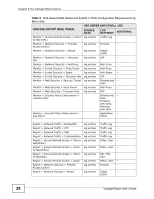
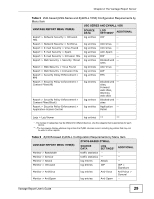
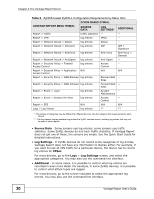
Chapter 2 The Vantage Report Server Table 6 ZyNOS-based ZyWALL Configuration Requirements by Menu Item VANTAGE REPORT MENU ITEM(S) ZYNOS-BASED ZYWALL SOURCE DATA LOG SETTINGS* ADDITIONAL Report > Traffic traffic statistics -- -- Report > VPN log entries IPSec -- Report > Network Attack > Attack log entries Attack -- Report > Network Attack > Intrusion log entries IDP IDP > Signature Report > Network Attack > AntiVirus log entries Anti-Virus Anti-Virus > General Report > Network Attack > AntiSpam log entries Anti-Spam -- Report > Security Policy > Firewall log entries Access -- Access Control Control Report > Security Policy > Application N/A Access Control N/A N/A Report > Security Policy > WEB Blocked log entries Blocked Web -Sites Report > Security Policy > WEB Allowed log entries Forward Web -Sites Report > Event > Login log entries System -- Maintenance Report > Event > Session Per Host log entries Access -- Control Report > EPS N/A N/A N/A Logs > Log Viewer log entries ** ** * - The names of categories may be different for different devices. Use the category that is appropriate for each device. ** - The log viewers display whatever log entries the ZyXEL devices record, including log entries that may not be used in other reports. • Source Data - Some screens use log entries; some screens use traffic statistics. Some ZyXEL devices do not track traffic statistics. If Vantage Report does not get one of these, the screens are empty. See the Quick Start Guide for detailed instructions. • Log Settings - If ZyXEL devices do not record some categories of log entries, Vantage Report does not have any information to display either. For example, if you want to look at VPN traffic for a particular device, the device has to record log entries for IPSec. For most devices, go to the Logs > Log Settings screen, and select the appropriate categories. You may also use the command-line interface. • Additional - In some cases, it is possible to control what log entries are recorded in even more detail. For example, in some ZyXEL devices, it is possible to control what attack types are logged. For most devices, go to the screen indicated to select the appropriate log entries. You may also use the command-line interface. 30 Vantage Report User's Guide