Cisco SRW2024P User Guide - Page 45
Security > Port Security
 |
UPC - 745883571000
View all Cisco SRW2024P manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 45 highlights
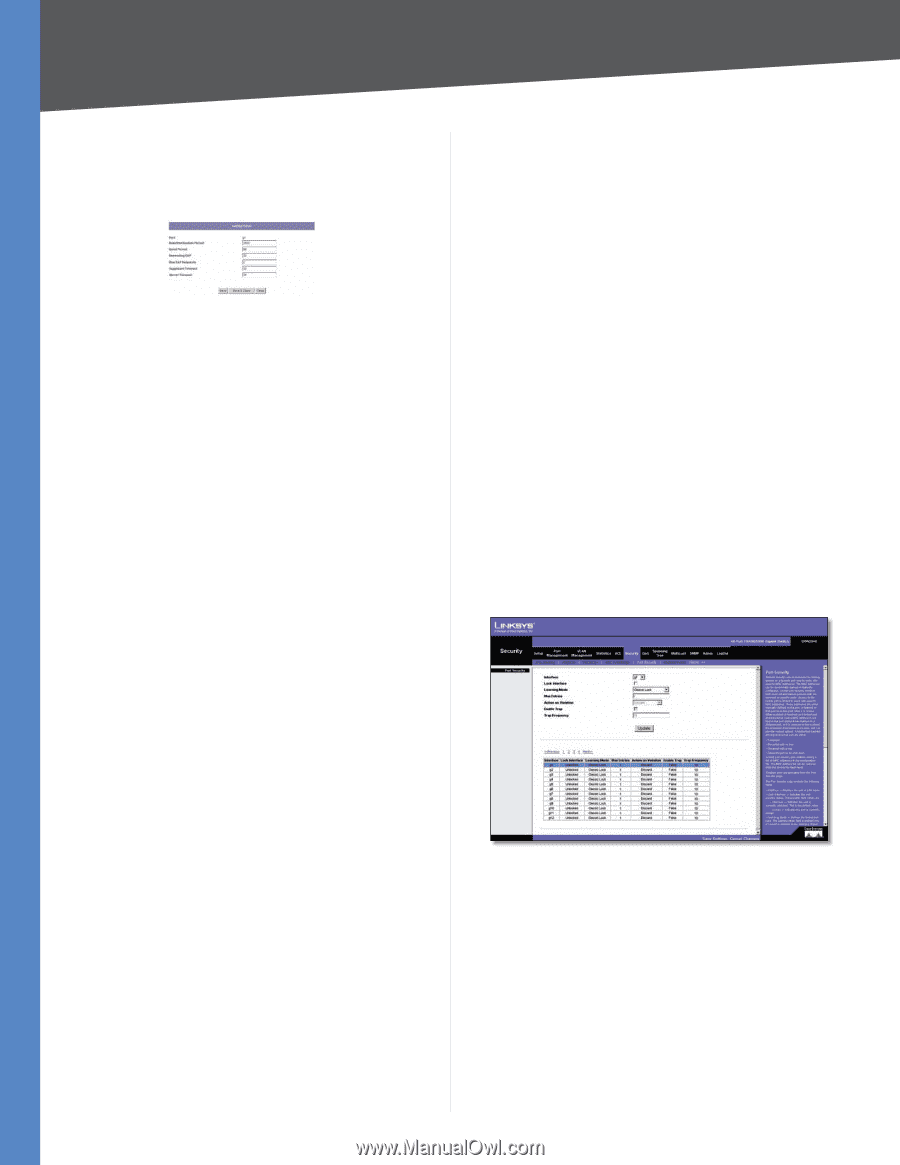
Chapter 5 Advanced Configuration Use the Setting Timer button to open the Setting Timer screen to configure ports for 802.1x functionality. 802.1x Settings > Setting Timer 802.1x Settings > Setting Timer Port Indicates the port name. Reauthentication Period Specifies the number of seconds in which the selected port is reauthenticated (Range: 300-4,294,967,295). The field default is 3600 seconds. Quiet Period Specifies the number of seconds that the switch remains in the quiet state following a failed authentication exchange (Range: 0-65,535). Resending EAP Specifies the number of seconds that the switch waits for a response to an EAP - request/identity frame, from the supplicant (client), before resending the request. Max EAP Requests Displays the total amount of EAP requests sent. If a response is not received after the defined period, the authentication process is restarted. The field default is 2 retries. SupplicantTimeout Displays the number of seconds that lapses before EAP requests are resent to the supplicant (Range: 1-65,535). The field default is 30 seconds. Server Timeout Specifies the number of seconds (1-65,535) that lapses before the switch resends a request to the authentication server. The default is 30 seconds. Security > Port Security Network security can be increased by limiting access on a specific port only to users with specific MAC addresses. MAC addresses can be dynamically learned or statically configured. Locked port security monitors both received and learned packets that are received on specific ports. Access to the locked port is limited to users with specific MAC addresses. These addresses are either manually defined on the port, or learned on that port up to the point when it is locked. When a packet is received on a locked port, and the packet source MAC address is not tied to that port (either it was learned on a different port, or it is unknown to the system), the protection mechanism is invoked, and can provide various options. Unauthorized packets arriving at a locked port are either: •• Forwarded •• Discarded with no trap •• Discarded with a trap •• Cause the port to be shut down. Locked port security also enables storing a list of MAC addresses in the configuration file. The MAC address list can be restored after the device has been reset. Disabled ports are activated from the Port Security page. Security > Port Security Interface Displays the port or LAG name. Lock Interface Selecting this option locks the specified interface. WebView Switches 38