Netgear WAG102 WAG102 Reference Manual - Page 102
WPA and WPA2 with RADIUS, WPA2 with RADIUS
 |
UPC - 606449028799
View all Netgear WAG102 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 102 highlights
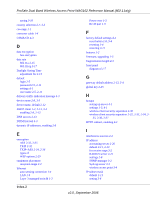
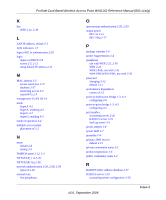
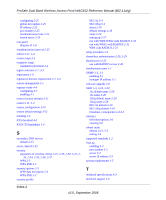
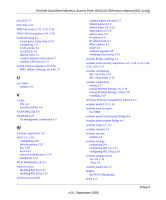
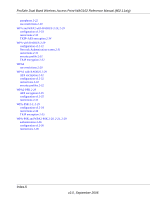
ProSafe Dual Band Wireless Access Point WAG102 Reference Manual (802.11a/g) passphrase 2-22 use restrictions 2-20 WPA and WPA2 with RADIUS 2-20, 2-29 configuration of 2-33 restrictions 2-33 TKIP+AES encryption 2-34 WPA with RADIUS 2-29 configuration of 2-31 Network Authentication screen 2-31 restrictions 2-31 security profile 2-31 TKIP encryption 2-32 WPA2 use restrictions 2-20 WPA2 with RADIUS 2-29 AES encryption 2-32 configuration of 2-32 restructions 2-32 security profiles 2-32 WPA2-PSK 2-29 AES encryption 2-35 configuration of 2-35 restrictions 2-35 WPA-PSK 2-3, 2-29 configuration of 2-34 restrictions 2-34 TKIP encryption 2-35 WPA-PSK and WPA2-PSK 2-20, 2-21, 2-29 authentication 2-36 configuration of 2-36 restructions 2-36 Index-6 v2.0, September 2006