Cisco 7921G Administration Guide - Page 23
Feature, Description, Cisco Unified IP Phone 7921G supports only the Secure Hash
 |
UPC - 882658123108
View all Cisco 7921G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 23 highlights
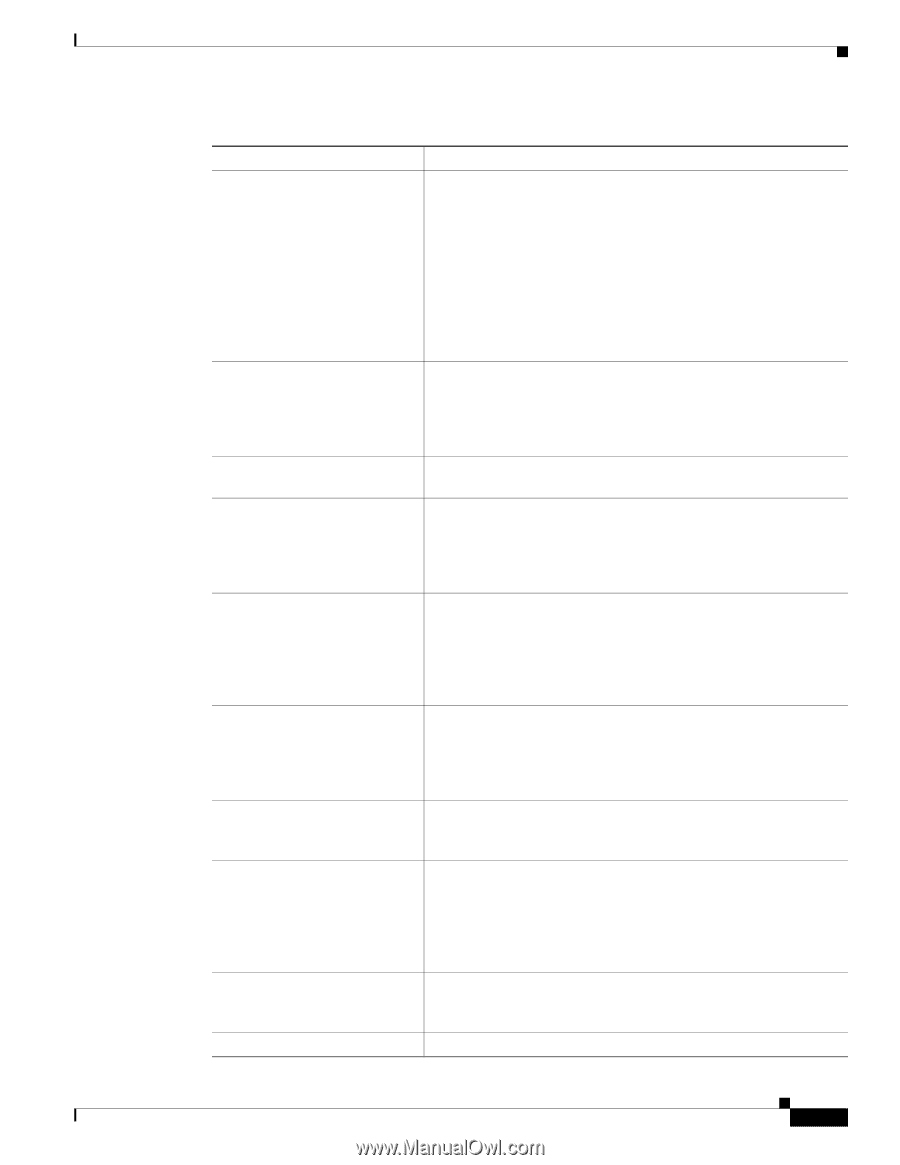
Chapter 1 Overview of the Cisco Unified Wireless IP Phone 7921G Understanding Security Features for Cisco Unified IP Phones OL-15985-01 Table 1-2 Overview of Security Features (continued) Feature Device authentication File authentication Signaling Authentication Manufacturing installed certificate Secure SRST reference Media encryption Signaling encryption CAPF (Certificate Authority Proxy Function) Security profiles Encrypted configuration files Description Occurs between the Cisco Unified Communications Manager server and the phone when each entity accepts the certificate of the other entity. Determines whether a secure connection between the phone and a Cisco Unified Communications Manager should occur, and, if necessary, creates a secure signaling path between the entities using TLS protocol. Cisco Unified Communications Manager will not register phones unless authenticated by the Cisco Unified Communications Manager. Cisco Unified IP Phone 7921G supports only the Secure Hash Algorithm-1 (SHA-1) signature algorithm. Validates digitally-signed files that the phone downloads. The phone validates the signature to make sure that file tampering did not occur after the file creation. Files that fail authentication are not written to Flash memory on the phone. The phone rejects such files without further processing. Uses the TLS protocol to validate that no tampering has occurred to signaling packets during transmission. Each Cisco Unified IP Phone contains a unique manufacturing installed certificate (MIC), which is used for device authentication. The MIC is a permanent unique proof of identity for the phone, and allows Cisco Unified Communications Manager to authenticate the phone. After you configure a SRST reference for security and then reset the dependent devices in Cisco Unified Communications Manager Administration, the TFTP server adds the SRST certificate to the phone cnf.xml file and sends the file to the phone. A secure phone then uses a TLS connection to interact with the SRST-enabled router. Uses SRTP to ensure that the media streams between supported devices proves secure and that only the intended device receives and reads the data. Includes creating a media master key pair for the devices, delivering the keys to the devices, and securing the delivery of the keys while the keys are in transport. Ensures that all SCCP signaling messages that are sent between the device and the Cisco Unified Communications Manager server are encrypted. Implements parts of the certificate generation procedure that are too processing-intensive for the phone, and it interacts with the phone for key generation and certificate installation. The CAPF can be configured to request certificates from customer-specified certificate authorities on behalf of the phone, or it can be configured to generate certificates locally. Defines whether the phone is non-secure, authenticated, or encrypted. See the "Understanding Security Profiles" section on page 1-10 for more information. Lets you ensure the privacy of phone configuration files. Cisco Unified Wireless IP Phone 7921G Administration Guide for Cisco Unified Communications Manager Release 7.0 1-9