Cisco CISCO1401 Software Guide - Page 133
RADIUS Operation
 |
UPC - 746320202785
View all Cisco CISCO1401 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 133 highlights
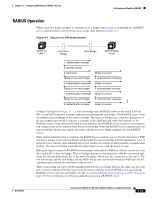
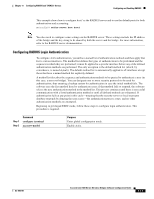
Chapter 11 Configuring RADIUS and TACACS+ Servers Configuring and Enabling RADIUS RADIUS Operation When a non-root bridge attempts to authenticate to a bridge whose access is controlled by a RADIUS server, authentication to the network occurs in the steps shown in Figure 11-1: Figure 11-1 Sequence for EAP Authentication OL-4059-01 Switch on LAN 1 Non-Root Bridge Root Bridge Authentication server 1. Authentication request 2. Identity request 3. Username (Relay to server) (Relay to non-root bridge) 4. Authentication challenge 5. Authentication response (Relay to server) (Relay to non-root bridge) 6. Authentication success 7. Authentication challenge (Relay to server) (Relay to non-root bridge) 8. Authentication response 9. Authentication success (Relay to server) 88901 In Steps 1 through 9 in Figure 11-1, a non-root bridge and a RADIUS server on the wired LAN use 802.1x and EAP to perform a mutual authentication through the root bridge. The RADIUS server sends an authentication challenge to the non-root bridge. The non-root bridge uses a one-way encryption of the user-supplied password to generate a response to the challenge and sends that response to the RADIUS server. Using information from its user database, the RADIUS server creates its own response and compares that to the response from the non-root bridge. When the RADIUS server authenticates the non-root bridge, the process repeats in reverse, and the non-root bridge authenticates the RADIUS server. When mutual authentication is complete, the RADIUS server and the non-root bridge determine a WEP key that is unique to the non-root bridge and provides the non-root bridge with the appropriate level of network access, thereby approximating the level of security in a wired switched segment to an individual desktop. The non-root bridge loads this key and prepares to use it for the logon session. During the logon session, the RADIUS server encrypts and sends the WEP key, called a session key, over the wired LAN to the root bridge. The root bridge encrypts its broadcast key with the session key and sends the encrypted broadcast key to the non-root bridge, which uses the session key to decrypt it. The non-root bridge and the root bridge activate WEP and use the session and broadcast WEP keys for all communications during the remainder of the session. There is more than one type of EAP authentication, but the root bridge behaves the same way for each type: it relays authentication messages from the non-root bridge to the RADIUS server and from the RADIUS server to the non-root bridge. See the "Assigning Authentication Types to an SSID" section on page 10-5 for instructions on setting up authentication using a RADIUS server. Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 11-3