Lenovo ThinkPad T40p IBM System Information Center Administrator's Guide - Page 20
Securing, network, Secure, Sockets, Layer, security
 |
View all Lenovo ThinkPad T40p manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 20 highlights
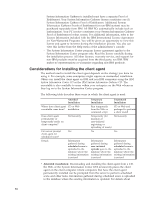
account password is required. If you mark this option, type information in the Minimum Windows password length and Maximum Windows password age fields. v Required antivirus application*: Mark this check box if you want the System Information Center program to check and verify that the required antivirus application is installed on all client computers each time the asset is revised. Type the name of the application in the Application field and the version number in the Version field of the required antivirus application (must appear in Windows Control Panel Add/Remove Programs list). Note: In the event that more than one antivirus program is used in your enterprise, you can modify the ISIC.PROPERTIES file to check computer assets for more than one antivirus program. For more information about modifying the ISIC.PROPERTIES file, see "Working with the ISIC.PROPERTIES file" on page 37. v Required firewall application*: Mark this check box if you want the System Information Center program to check and verify that the required firewall application is installed on all client computers each time the asset is revised. Type the name of the application in the Application field and the version number in the Version field of the required firewall application (must appear in Windows Control Panel Add/Remove Programs list). Note: In the event that more than one firewall application is used in your enterprise, you can modify the ISIC.PROPERTIES file to check computer assets for more than one firewall application. For more information about modifying the ISIC.PROPERTIES file, see "Working with the ISIC.PROPERTIES file" on page 37. 14. Click Next. The Ready to Install window opens. 15. Click Next. The Setup Status window opens and the progress indicator displays the progress of the setup. After completing, the ″Restart required to complete installation″ window opens. 16. Mark an option button to restart your computer now or restart later. Click Finish. 17. If you have chosen to restart your computer, close any open programs and remove any disks from their drives; your computer will shut down and restart. This concludes the installation of the System Information Center program on a server. Note: After you install the System Information Center program, the first user account you will create will be the Administrator account. Once you have created that account, you can manually add a User account or change the authority of a User account. A User can create their own account by registering assets. For more information, see "Creating accounts" on page 22. Securing your network with Secure Sockets Layer (SSL) security In most cases, you do not need SSL. However, if your clients communicate with the server using the Internet and are not protected by a firewall, the communication will require encryption. You will need to: 1. Modify the ISIC.PROPERTIES file by replacing all occurrences of HTTP:// with HTTPS://. (For more information, see Appendix A, "Modifying the ISIC.PROPERTIES file," on page 51.) 12