HP 635n HP Jetdirect Print Servers - How to Use 802.1X on HP Jetdirect Print S - Page 2
Introduction
 |
UPC - 882780301016
View all HP 635n manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 2 highlights
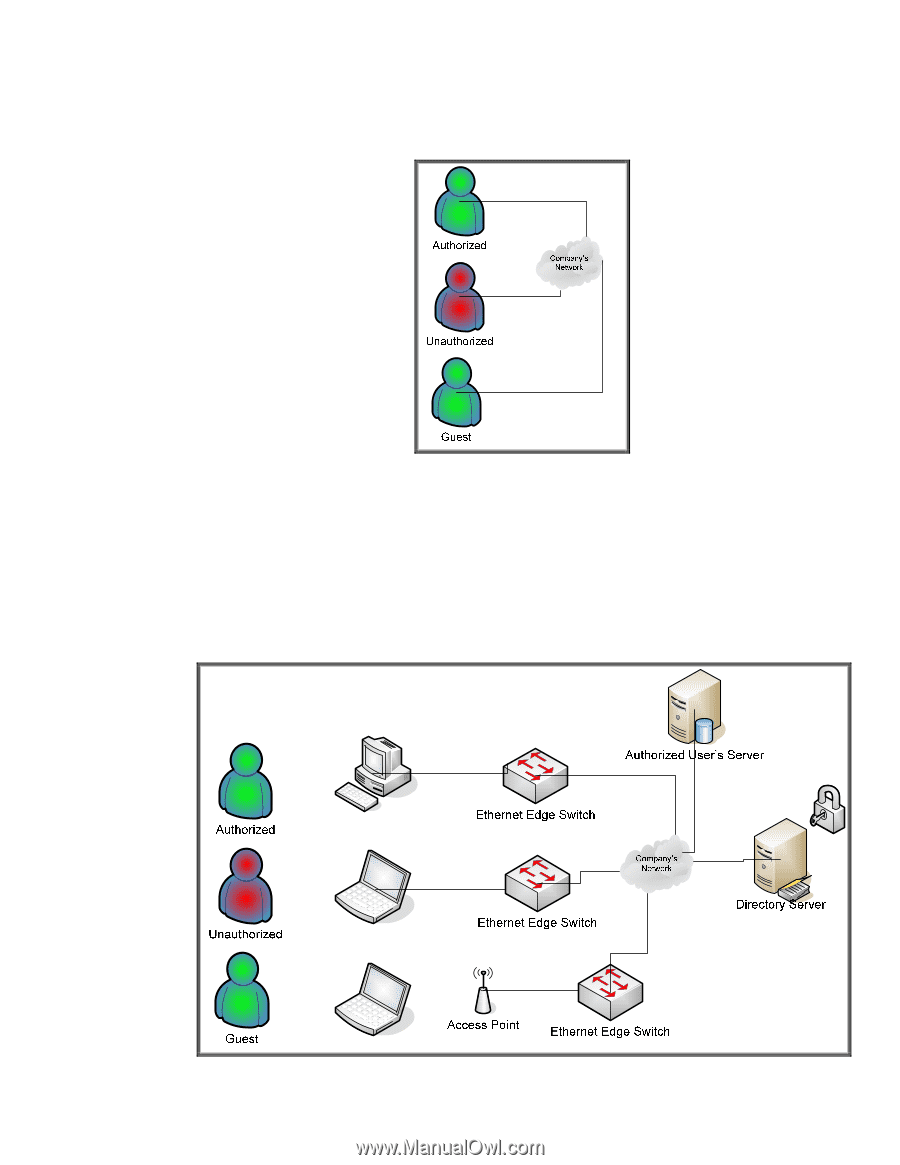
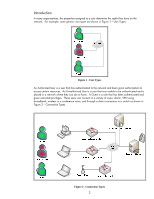
Introduction In many organizations, the properties assigned to a user determine the rights they have on the network. For example, some generic user types are shown in Figure 1 - User Types: Figure 1 - User Types An Authorized User is a user that has authenticated to the network and been given authorization to access certain resources. An Unauthorized User is a user that was unable to be authenticated and is placed in a network where they can do no harm. A Guest is a user that has been authenticated and given restricted privileges. These users can connect in a variety of ways: dial-in, VPN using broadband, wireless in a conference room, and through a direct connection to a switch as shown in Figure 2 - Connection Types. Figure 2 - Connection Types 2