TP-Link TL-SL5428E User Guide - Page 48
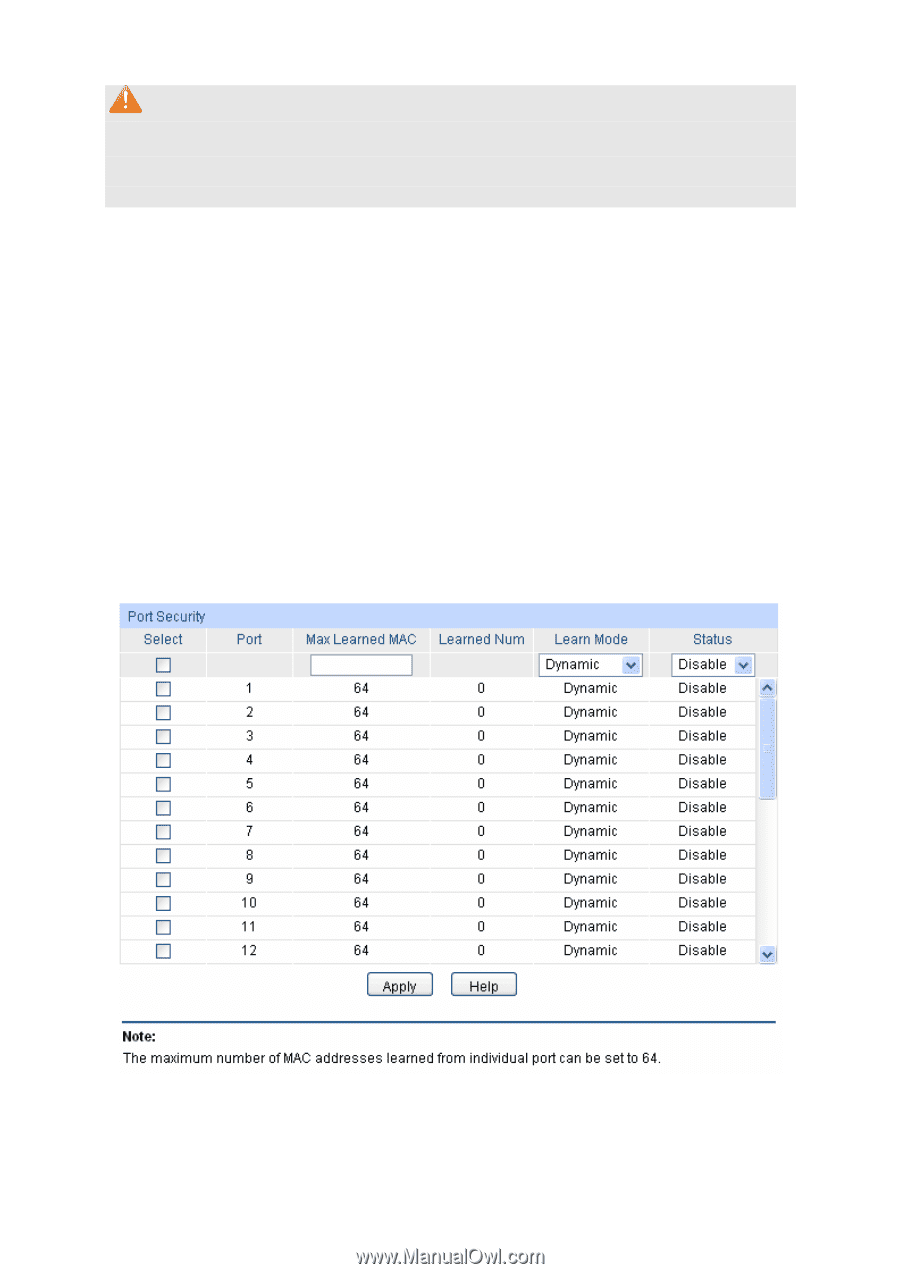
Port Security
 |
UPC - 845973020873
View all TP-Link TL-SL5428E manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 48 highlights
Note: 1. The LAG member can not be selected as the mirrored port or mirroring port. 2. A port can not be set as the mirrored port and the mirroring port simultaneously. 3. The Port Mirror function can take effect span the multiple VLANs. 7.1.3 Port Security MAC Address Table maintains the mapping relationship between the port and the MAC address of the connected device, which is the base of the packet forwarding. The capacity of MAC Address Table is fixed. MAC Address Attack is the attack method that the attacker takes to obtain the network information illegally. The attacker uses tools to generate the cheating MAC address and quickly occupy the MAC Address Table. When the MAC Address Table is full, the switch will broadcast the packets to all the ports. At this moment, the attacker can obtain the network information via various sniffers and attacks. When the MAC Address Table is full, the packets traffic will flood to all the ports, which results in overload, lower speed, packets drop and even breakdown of the system. Port Security is to protect the switch from the malicious MAC Address Attack by limiting the maximum number of MAC addresses that can be learned on the port. The port with Port Security feature enabled will learn the MAC address dynamically. When the learned MAC address number reaches the maximum, the port will stop learning. Thereafter, the other devices with the MAC address unlearned can not access to the network via this port. Choose the menu Switching→Port→Port Security to load the following page. Figure 7-3 Port Security The following entries are displayed on this screen: ¾ Port Security 40